|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows >> CuteFTP multiple flaws Vulnerability Assessment Details
|
CuteFTP multiple flaws |
||
|
Acertains the presence of CuteFTP.exe Detailed Explanation for this Vulnerability Assessment The remote host has the program CuteFTP.exe installed. CuteFTP is a FTP client which contains two overflow conditions which may be exploited by a possible hacker to gain a shell on this host. To exploit these vulnerabilities, a possible hacker would need to set up a rogue FTP server and lure a user of this host to browse it using CuteFTP. Solution : Upgrade to CuteFTP 5.0.2.0 or newer Network Security Threat Level: High Networks Security ID: 6642, 6786 Vulnerability Assessment Copyright: This script is Copyright (C) 2003-2007 Tenable Network Security |
||
|
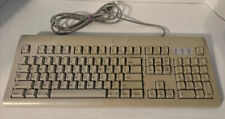
Cables, Connectors |

Vintage 1999 Apple Keyboard II Mac M0487 Excellent Condition Needs PS2 Cables
$250.00
Vintage Apple ImageWriter Printer ~A9M0303 *BROKEN KNOB, POWERS UP, NOT TESTED*
$47.99
Vintage Apple Newton MessagePad 2000 With Original Box and Some Accessories
$199.99
Vintage Apple Lisa Brochure, very nice condition
$50.00
Vintage Apple M2980 AppleDesign Keyboard - Tested and working - Good condition
$19.75
Rare Vintage Miniscribe Apple Macintosh SE / 20 8425SA 21MB 3.5" Drive Board
$29.99
Vintage APPLE Design Macintosh Keyboard Model M2980 UNTESTED
$32.97
Vintage A3S2 Apple III Computer With 12 Volt Motherboard 820-0043-00
$450.00
Apple Macintosh Performa 466 Vintage Computer | SKU 146754
$149.95
Apple Macintosh PowerBook 180 Vintage Laptop | Retro Computer
$149.95
|
||
|
No Discussions have been posted on this vulnerability. |