|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> smb2www remote command execution Vulnerability Assessment Details
|
smb2www remote command execution |
||
|
smb2www Command Execution Detailed Explanation for this Vulnerability Assessment The remote host is running smb2www - a SMB to WWW gateway. There is a flaw in the version of this CGI which permits anyone to execute arbitrary commands on this host by sending a malformed argument to smbshr.pl, one of the components of this solution. Solution : Upgrade to the latest version Network Security Threat Level: High Networks Security ID: 6313 Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Renaud Deraison |
||
|
Cables, Connectors |

Vintage Apple IIe (2e) Computer, monitor, joystick, cooling fan, floppy set
$329.00
VINTAGE APPLE Macintosh Performa 6400/180 Desktop Computer (M3548) - CHIMES
$79.99
Vintage Apple III Brochure for BPI Accounting Series, very nice condition
$50.00
Vintage Apple Computer Monitor
$45.90
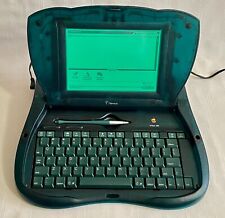
Vintage Apple Newton eMate 300 Laptop Computer 1997 H0208 Teal Blue Green Last 1
$194.99
Vintage Apple M2980 AppleDesign Keyboard - Tested and working - Good condition
$19.75
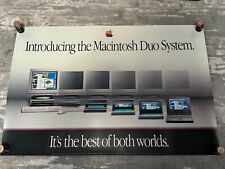
Vintage Apple "Introducing the Macintosh Duo System" Poster
$100.00
Vintage Apple Powerbook G4 12 inch 512MB memory 1.5ghz 80gb Hd
$68.00
Vintage Apple Keyboard & Mouse Translucent Blue M2452/M4848 Good Condition
$49.95
Vintage Apple M7803 Pro USB Wired Keyboard Clear Black 2000
$24.99
|
||
|
No Discussions have been posted on this vulnerability. |