|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Denial of Service >> rfparalyze Vulnerability Assessment Details
|
rfparalyze |
||
|
Crash a host through winpopups Detailed Explanation for this Vulnerability Assessment It was possible to crash the remote host using the 'rfparalyze' denial of service attack. Solution : contact Microsoft for a patch. Meanwhile, filter incoming tcp connections to this port Network Security Threat Level: High Networks Security ID: 1163 Vulnerability Assessment Copyright: This script is Copyright (C) 2000 Renaud Deraison. Orignal code RFP |
||
|
Cables, Connectors |

Cisco SG95-16 16-Port Gigabit Switch SG95-16-KR
$47.00
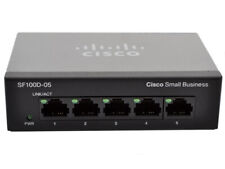
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
Cisco Meraki MS120-48LP 48 Port Blade Ethernet Switch UNCLAIMED
$799.00
Aruba 7030-US Wireless LAN Mobility Controller ARCN7030
$74.95
New Linksys SE3005 5-port Gigabit Ethernet Switch
$18.99
HP 2530-48G 48 Port Gigabit Ethernet Network Switch J9775A
$30.95
Linksys SE3008 8 Ports Rack Mountable Gigabit Ethernet Switch
$21.99
NetGear ProSafe GS748T V4 48-Port Gigabit Smart Switch w/ Ears + Cord
$35.00
HP JG937A Flexnetwork 5130-48G PoE+ 48-Port Gigabit Network Switch
$65.95
HP ProCurve 2530-24G J9776A 24 Port Gigabit Ethernet Managed Network Switch
$34.99
|
||
|
No Discussions have been posted on this vulnerability. |