|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> php.cgi buffer overrun Vulnerability Assessment Details
|
php.cgi buffer overrun |
||
|
Checks for the /cgi-bin/php.cgi buffer overrun Detailed Explanation for this Vulnerability Assessment There is a buffer overrun in the 'php.cgi' CGI program, which will permit anyone to execute arbitrary commands with the same rights as the web server (root or nobody). Solution : remove it from /cgi-bin. Network Security Threat Level: High Networks Security ID: 712 Vulnerability Assessment Copyright: This script is Copyright (C) 1999 Renaud Deraison |
||
|
Cables, Connectors |

Toshiba 512GB SSD Solid State Drive 2.5" SATA THNSNC512GBSJ Sun Oracle 7010845
$53.99
Dell - 800GB SSD SAS 12G MLC WI 2.5in PX05SM CN3JH
$98.99
Dell - 2TTK9 640GB Fusion iO Drive PCI-E Flash SSD
$62.99
Dell PowerEdge R630 Server | 2x E5-2680v3 24 Cores | H730 | Choose RAM/DRIVES
$1635.00
Patriot P210 128GB 256GB 512GB 1TB 2TB 2.5" SATA 3 6GB/s Internal SSD PC/MAC Lot
$14.99
Intel DC S3510 Series 120GB SSD 2.5" 6Gb/s SATA Solid State Drive SSDSC2BB120G6K
$9.99
Netac 1TB 2TB 512GB Internal SSD 2.5'' SATA III 6Gb/s Solid State Drive lot
$13.99
Fanxiang SSD 512GB 1TB 2TB 4TB 2.5'' SSD SATA III Internal Solid State Drive lot
$13.99
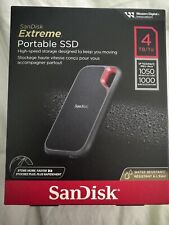
SanDisk Extreme Portable 4TB USB-C SSD Black SDSSDE61-4T00
$214.99
Fanxiang 4TB 2TB 1TB SSD 550MB/s 2.5'' SATA III Internal Solid State Drive lot
$209.99
|
||
|
No Discussions have been posted on this vulnerability. |