|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> php < 4.3.3 Vulnerability Assessment Details
|
php < 4.3.3 |
||
|
Checks for version of PHP Detailed Explanation for this Vulnerability Assessment The remote host is running a version of PHP 4.3 which is older or equal to 4.3.2. There is a flaw in this version which may permit a local attacker to bypass the safe mode and gain unauthorized access to files on the local system, thanks to a flaw in the function php_safe_mode_include_dir(). Solution : Upgrade to PHP 4.3.3 when it is available Network Security Threat Level: Medium Networks Security ID: 8201 Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Renaud Deraison |
||
|
Cables, Connectors |

Apple Macintosh Plus 1Mb Vintage Desktop Computer
$149.99
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Z80 - NABU PC & Keyboard - Vintage New Old Stock (Retro 80's)
$139.99
Vintage SGI Silicon Graphics 1600SW Flat Panel Monitor & Multilink Adapter
$699.00
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Vintage SGI Silicon Graphics F180 Flat Panel Display Monitor CMN014/061-0053-001
$499.00
Vintage IBM 5150 5160 Personal Computer PC XT Drive cover Factory
$79.99
Vintage Black Microsoft intellimouse Optical USB Wheel Mouse 1.1/1.1a - EXC COND
$28.95
SEALED Vintage Western Digital Value Line Hard Drive 3.5-Inch Enhanced IDE 25 GB
$100.00
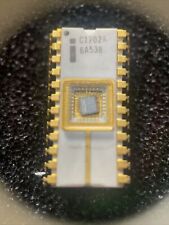
Vintage Computer Chip Gold White Ceramic Intel C1702A Static EPROM 2048-bit 1972
$95.00
|
||
|
No Discussions have been posted on this vulnerability. |