|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Denial of Service >> osTicket Support Address DoS Vulnerability Assessment Details
|
osTicket Support Address DoS |
||
|
Checks for Support Address DoS osTicket Detailed Explanation for this Vulnerability Assessment The target is running at least one instance of osTicket 1.2.7 or earlier. Such versions are subject to a denial of service attack in open.php if osTicket is configured to receive mails using aliases. If so, a remote attacker can generate a mail loop on the target by opening a ticket with the support address as the contact email address. For details, see : - http://www.osticket.com/forums/showthread.php?t=301 ***** Nessus has acertaind the vulnerability exists on the target ***** simply by looking at the version number(s) of osTicket installed ***** there. It has no way of knowing which method osTicket uses to ***** retrieve mail. Solution : Configure osTicket to receive mail using POP3. Network Security Threat Level: None / High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 George A. Theall |
||
|
Cables, Connectors |

Computer Lab International 122 Key Vintage Keyboard PS/2 TESTED
$88.88
Vintage Apple Mac Sony MP-F75W-01G 2MB 3.5" Floppy Disk Drive Parts Or Repair
$35.99
Vintage Apple Macintosh Power Supply Part Number 631-5105-A
$39.99
Vintage 1991 Hewlett Packard DeskJet 500 Printer Manual Bundle W Floppy Disk
$23.99
KIM Uno, an Arduino Pro Mini emulated Vintage MOS 6502 KIM-1 clone.
$50.00
Vintage 1980s IBM PC Jr Model 4860 Desktop Tower Computer W/2 EXPANSIONS
$100.00
Vintage Mountain FileSafe 7500 NCE External Tape Drive - No Cables - Untested
$29.99
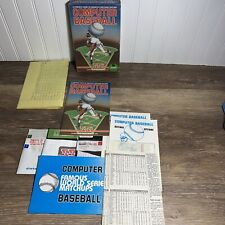
Vintage COMPUTER BASEBALL GAME- SSI- Retro- 48k Atari, Commodore 64 Floppy Disk
$35.00
Junk Drawer Vintage 1991 Adobe Type Manager Floppy Disk Lot of 3 - For Apple Mac
$40.00
VINTAGE 1992 NEWPORT SYSTEMS 700-0002-001 REV E GREAT CONDITION
$99.99
|
||
|
No Discussions have been posted on this vulnerability. |