|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> osTicket <= 1.2.7 Multiple Vulnerabilities Vulnerability Assessment Details
|
osTicket <= 1.2.7 Multiple Vulnerabilities |
||
|
Checks for multiple vulnerabilities in osTicket <= 1.2.7 Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a PHP application that is prone to multiple vulnerabilities. Description : The version of osTicket installed on the remote host suffers from several vulnerabilities, including: - A Remote File Include Vulnerability The script 'include/main.php' lets a possible hacker read arbitrary files on the remote host and possibly even run arbitrary PHP code, subject to the rights of the web server user. - Two SQL Injection Vulnerabilities An authenticated attacker can affect SQL queries through the 'id' parameter of the 'admin.php' script as well as the 'cat' parameter of the 'view.php' script. - Multiple Cross-Site Scripting Vulnerabilities osTicket does not properly sanitize user-supplied input in several scripts, which could facilitate the theft of cookie-based authentication credentials within the context of the affected website. - A Directory Traversal Vulnerability The 'attachments.php' script may let an authenticated attacker read arbitrary files on the remote, subject to the rights of the server user. This occurs only if attachment uploads have been specificall enabled by the administrator. See also : http://www.gulftech.org/?node=research&article_id=00071-05022005 http://archives.neohapsis.com/archives/bugtraq/2005-05/0051.html http://www.osticket.com/forums/showthread.php?t=1333 Solution : Upgrade to osTicket version 1.3.1 or later. Network Security Threat Level: Medium / CVSS Base Score : 6 (AV:R/AC:H/Au:NR/C:P/A:P/I:P/B:N) Networks Security ID: 13478 Vulnerability Assessment Copyright: This script is Copyright (C) 2005-2006 Tenable Network Security |
||
|
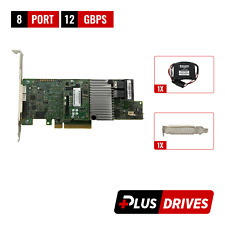
Cables, Connectors |

ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
HPE 727263-003 BL460c G9 Raid BBWC Smartstorage Battery
$24.99
HPE 869102-001 Smart Array E208i-a SR Gen10 Storage Controller RAID SP: 871039
$116.99
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
4 Bay RAID External Hard Drive Enclosure for 2.5/3.5" SATA HDD/SSD
$79.99
2 Bay RAID Hard Drive Enclosure USB 3.0 Type-B for 2.5" SATA SSD/HDD Enclosure
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |