|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> myBloggie Multiple Vulnerabilities Vulnerability Assessment Details
|
myBloggie Multiple Vulnerabilities |
||
|
Searches for the existence of a myBloggie Detailed Explanation for this Vulnerability Assessment The remote host is running myBloggie, a web log system written in PHP. The remote version of this software has been found contain multiple vulnerabilities: * Full Path Disclosure Due to an improper sanitization of the post_id parameter, it's possible to show the full path by sending a simple request. * Cross-Site Scripting (XSS) Input passed to 'year' parameter in viewmode.php is not properly sanitised before being returned to users. This can be exploited execute arbitrary HTML and script code in a user's browser session in context of a vulnerable site. * SQL Injection When myBloggie get the value of the 'keyword' parameter and put it in the SQL query, don't sanitise it. So a remote user can do SQL injection attacks. Solution: Patches have been provided by the vendor and are available at: http://mywebland.com/forums/viewtopic.php?t=180 Risk factor: High Networks Security ID: 13192, 13507 Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Noam Rathaus |
||
|
Cables, Connectors |

Vintage 5362 IBM System/36 Mini-Computer Mainframe 5291 2, CRT Terminal DM12N501
$249.99
Magitronic Quad Speed Creative
$150.00
Vintage Family owned Atari 1200xl computer sold as is tested turns on with cable
$299.99
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection - UNTESTED
$65.00
IBM 3390 DASD Hard Drive 10.8” from Vintage Mainframe
$325.00
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection
$130.99
VINTAGE IBM Type 4869 External 5 1/4" ~ Floppy Disk Drive Mainframe ~
$159.99
Cray Research Supercomputer Cray X-MP ECL Logic Board
$149.99
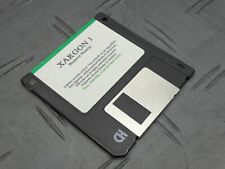
Xargon 1 Beyond Reality RARE Game Floppy 3.5” Floppy Mainframe Collection
$349.99
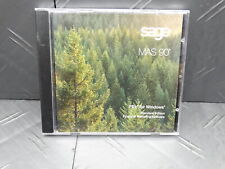
Sage MAS 90 Software for Windows Financial Reporting Mainframe Collection
$339.99
|
||
|
No Discussions have been posted on this vulnerability. |