|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain root remotely >> cfengine format string vulnerability Vulnerability Assessment Details
|
cfengine format string vulnerability |
||
|
check for cfengine flaw based on its version Detailed Explanation for this Vulnerability Assessment Cfengine is running on this remote host. Cfengine contains a component, cfd, which serves as a remote-configuration client to cfengine. This version of cfd contains several flaws in the way that it calls syslog(). As a result, trusted hosts and valid users (if access controls are not in place) can cause the vulnerable host to log malicious data which, when logged, can either crash the server or execute arbitrary code on the stack. In the latter case, the code would be executed as the 'root' user. Solution: Upgrade to 1.6.0a11 or newer Network Security Threat Level: High Networks Security ID: 1757 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 David Maciejak |
||
|
Cables, Connectors |

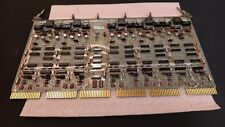
Vintage DEC/CLEARPOINT INC. -QRAM-2 SAB-1 1MB Q-BUS MEMORY MSV11-QA (B2)
$129.99
Vintage DEC DECserver 250 Motorola 68000 print server ST534
$30.00
DEC VINTAGE DIGITAL EQUIPMENT CORPORATION VT100 TERMINAL & KEYBOARD AS-IS
$198.99
DEC PDP 8/M PDP 8M / 4 avail / Vintage Digital Equipment Corp /Also DEC PDP 12
$5775.00
DEC DIGITAL Equipment Corp VT220-D2 Vintage CRT Terminal
$215.00
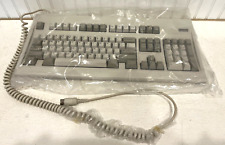
Digital Equipment Corporation DEC-2000 Vintage Keyboard - NOS NEW in Plastic
$119.95
Vintage Digital DEC dfo1 Acoustic Coupler modem Anderson Jacobsen Mod# A242 RARE
$189.95
Rare Vintage DEC DIGITAL DFO3 modem with manual Powers up but UNTESTED
$69.95
Vintage DEC Digital VR201 Computer Monitor AS IS
$249.95
Vintage DEC Digital Equipment Corp PDP 11/40 G114 16K SENSE/INHIBIT (B10)
$269.99
|
||
|
No Discussions have been posted on this vulnerability. |