|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> NIS >> bootparamd service Vulnerability Assessment Details
|
bootparamd service |
||
|
Checks the presence of a RPC service Detailed Explanation for this Vulnerability Assessment The bootparamd RPC service is running. It is used by diskless clients to get the necessary information needed to boot properly. If a possible hacker uses the BOOTPARAMPROC_WHOAMI and provides the correct address of the client, then he will get its NIS domain back from the server. Once the attacker discovers the NIS domain name, it may easily get your NIS password file. Solution : filter incoming traffic to prevent connections to the portmapper and to the bootparam daemon, or deactivate this service if you do not use it. Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 1999 Renaud Deraison |
||
|
Cables, Connectors |

Vintage Apple M2980 AppleDesign Keyboard - Tested and working - Good condition
$19.75
Vintage Apple IIe (2e) Computer, monitor, joystick, cooling fan, floppy set
$250.00
Vintage Apple Power Macintosh 5400/200 M3046 Computer -Keyboard Mouse Parts Only
$125.00
Vintage Apple III Brochure for BPI Accounting Series, very nice condition
$50.00
VINTAGE Apple External SCSI CD-ROM Disk Drive AppleCD 600e POWERS ON
$69.99
VTG Apple Macintosh Plus 1Mb - UNTESTED
$70.00
Vintage Apple Computer Monitor
$45.90
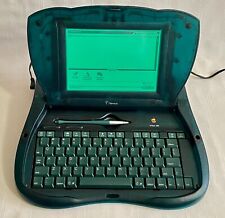
Vintage Apple Newton eMate 300 Laptop Computer 1997 H0208 Teal Blue Green Last 1
$194.99
Vintage Apple Keyboard & Mouse Translucent Blue M2452/M4848 Good Condition
$49.95
Vintage Apple M7803 Pro USB Wired Keyboard Clear Black 2000
$24.99
|
||
|
No Discussions have been posted on this vulnerability. |