|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Firewalls >> ZoneAlarm Personal Firewall port 67 flaw Vulnerability Assessment Details
|
ZoneAlarm Personal Firewall port 67 flaw |
||
|
Check ZoneAlarm version Detailed Explanation for this Vulnerability Assessment ZoneAlarm firewall runs on this host. This version contains a flaw that may permit a remote attacker to bypass the ruleset. The issue is due to ZoneAlarm not monitoring and alerting UDP traffic with a source port of 67. This permits a possible hacker to bypass the firewall to reach protected hosts without setting off warnings on the firewall. Solution : Upgrade at least to version 2.1.25 Network Security Threat Level: High Networks Security ID: 1137 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 David Maciejak |
||
|
Cables, Connectors |

$6.24
Vintage P51430TX TITANIUM I B+
$99.00
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
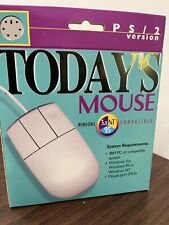
Vintage Computer Mouse - Todays Mouse - Windows 95 P S/2
$9.99
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Z80 - NABU PC & Keyboard - Vintage New Old Stock (Retro 80's)
$139.99
Vintage Black Microsoft intellimouse Optical USB Wheel Mouse 1.1/1.1a - EXC COND
$28.95
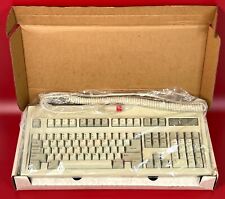
Vintage NOS Keytronic E03601Q AT/XT 5 Pin DIN Wired Computer Keyboard, SEALED
$89.99
VINTAGE APPLE Macintosh PowerBook 3400C M3553 UNTESTED AS IS
$135.60
|
||
|
No Discussions have been posted on this vulnerability. |