|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows >> WinGate Compressed Name Pointer Denial of Service Vulnerability Vulnerability Assessment Details
|
WinGate Compressed Name Pointer Denial of Service Vulnerability |
||
|
Checks version number in WinGate's banner Detailed Explanation for this Vulnerability Assessment Summary : The remote proxy is affected by a denial of service vulnerability. Description : The remote host appears to be running WinGate, a Windows application for managing and securing Internet access. The version of WinGate installed on the remote host contains a flaw involving the processing of DNS requests with compressed name pointers. By sending a specially-crafted DNS request to a UDP port on which WinGate is listening, an unauthenticated remote attacker can cause the affected application to consume 100% of the available CPU, thereby denying service to legitimate users. See also : http://labs.idefense.com/intelligence/vulnerabilities/display.php?id=444 http://archives.neohapsis.com/archives/fulldisclosure/2006-11/0398.html http://forums.qbik.com/viewtopic.php?t=4215 Solution : Upgrade to WinGate 6.2.0 or later. Network Security Threat Level: Low / CVSS Base Score : 2.3 (AV:R/AC:L/Au:NR/C:N/I:N/A:P/B:N) Networks Security ID: 21295 Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Cisco ASA 5520 Adaptive Security Appliance
$56.75
NetFu Firewall 1U, Intel CPU, 8 x Gigabit, SFP, w/ pfSense, Others, NEW OPTIONS
$541.85
Cisco FPR2130-NGFW-K9 Firepower 2130 Security Appliance 1 Year Warranty
$3550.00
Fortinet Fortigate FG-61E | Firewall Network Security Appliance
$49.99
Fortinet FortiGate FG-40F Network Security Firewall
$100.00
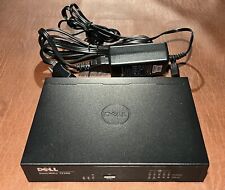
Dell SonicWall TZ300 5-Port Network Security Firewall Appliance APL28-0B4
$24.95
Fortinet Fortigate 70D Firewall Adapter Network Security Appliance
$52.00
OPNsense six-port Gigabit router/firewall on Lanner FW-7535 hardware
$69.00
Fortinet Fortiwifi 60D FG-60D Security Appliance Firewall / VPN w/ AC Adapter
$999.97
Fortinet FortiGate 60E & FortiAP 221E+ Network Security Firewall
$260.00
|
||
|
No Discussions have been posted on this vulnerability. |