|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> WebGUI < 6.7.6 arbitrary command execution Vulnerability Assessment Details
|
WebGUI < 6.7.6 arbitrary command execution |
||
|
Checks for arbitrary remote command execution in WebGUI < 6.7.6 Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a CGI script that is prone to arbitrary code execution. Description : The remote host is running WebGUI, a content management system from Plain Black Software. The installed version of WebGUI on the remote host fails to sanitize user-supplied input via the 'class' variable to various sources before using it to run commands. By leveraging this flaw, a possible hacker may be able to execute arbitrary commands on the remote host within the context of the affected web server userid. See also : http://www.plainblack.com/getwebgui/advisories/security-exploit-patch-for-6.3-and-above Solution : Upgrade to WebGUI 6.7.6 or later. Network Security Threat Level: High / CVSS Base Score : 7 (AV:R/AC:L/Au:NR/C:P/A:P/I:P/B:N) Networks Security ID: 15083 Vulnerability Assessment Copyright: This script is Copyright (C) 2005 David Maciejak |
||
|
Cables, Connectors |

Vintage 5362 IBM System/36 Mini-Computer Mainframe 5291 2, CRT Terminal DM12N501
$249.99
Vintage Family owned Atari 1200xl computer sold as is tested turns on with cable
$299.99
Magitronic Quad Speed Creative
$150.00
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection - UNTESTED
$65.00
IBM 3390 DASD Hard Drive 10.8” from Vintage Mainframe
$325.00
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection
$130.99
VINTAGE IBM Type 4869 External 5 1/4" ~ Floppy Disk Drive Mainframe ~
$159.99
Cray Research Supercomputer Cray X-MP ECL Logic Board
$149.99
IVIS Mainframe Mechanical Keyboard RJ11 Wired Keyboard Mainframe Collection
$584.99
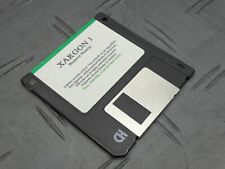
Xargon 1 Beyond Reality RARE Game Floppy 3.5” Floppy Mainframe Collection
$349.99
|
||
|
No Discussions have been posted on this vulnerability. |