|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> WebAPP Directory Traversal Vulnerability Assessment Details
|
WebAPP Directory Traversal |
||
|
Checks for a directory traversal bug in WebAPP Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a CGI script that is susceptible to directory traversal attacks. Description : There is a flaw in the remote version of WebApp fails to filter directory traversal sequences from the 'viewcat' parameter of the 'index.cgi' script. An unauthenticated attacker can leverage this issue to read arbitrary files on the remote host with the rights of the web server process. See also : http://marc.theaimsgroup.com/?l=bugtraq&m=109336268002879&w=2 http://cornerstone.web-app.org/cgi-bin/index.cgi?action=downloads&cat=updates Solution : Apply the fix provided by the vendor. Risk factor: Low / CVSS Base Score : 2 (AV:R/AC:L/Au:NR/C:P/A:N/I:N/B:N) Networks Security ID: 11028 Vulnerability Assessment Copyright: This script is Copyright (C) 2004-2006 Tenable Network Security |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Samsung PM983a M.2 22110 SSD NVMe PCIe 3.0x4 1.88TB
$88.50
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung - S Pen Creator Edition - White
$40.00
Samsung Galaxy Chromebook Go, 14-inch, 32GB, Unlocked All Carriers - Silver
$99.95
Samsung PM983 SSD M.2 22110 NVMe PCIe 3.0x4 1.88TB
$86.50
Samsung Galaxy 12.4 Inch EF-DT730 Slim Keyboard For S7+ | S7 FE | S8+ | S8+ 5G
$39.99
Samsung 16GB 2Rx4 PC3-12800R M393B2G70BH0-CK0 DDR3 RDIMM - SERVER RAM
$8.90
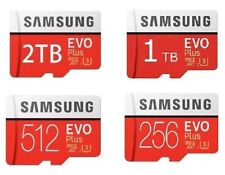
512GB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$21.99
|
||
|
No Discussions have been posted on this vulnerability. |