|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows >> WINS Buffer Overflow (830352 - netbios check) Vulnerability Assessment Details
|
WINS Buffer Overflow (830352 - netbios check) |
||
|
Acertains if hotfix 830352 has been installed (Netbios) Detailed Explanation for this Vulnerability Assessment Summary : Arbitrary code can be executed on the remote host. Description : The remote Windows Internet Naming Service (WINS) is vulnerable to a flaw which could permit a possible hacker to execute arbitrary code on this host. To exploit this flaw, a possible hacker would need to send a specially crafted packet with improperly advertised lengths. Solution : http://www.microsoft.com/technet/security/bulletin/MS04-006.mspx Network Security Threat Level: Critical / CVSS Base Score : 10 (AV:R/AC:L/Au:NR/C:C/A:C/I:C/B:N) Networks Security ID: 9624 Vulnerability Assessment Copyright: This script is Copyright (C) 2004-2006 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Dream Writer NTS 325 Computer Basic Language Notebook “Untested “
$30.00
Vintage Sun SunBlade 100 Workstation UltraSPARC IIe 1.6GB 20GB HD 380-0467-01
$150.00
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Datacomp DCK 84 BRAND NEW Vintage Keyboard
$39.00
Vintage Apple LisaDraw Brochure, very nice condition
$40.00
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
M&M's Data Pro Organizer Touch Screen With Pen Vintage RARE FIND NEW SEALED
$45.00
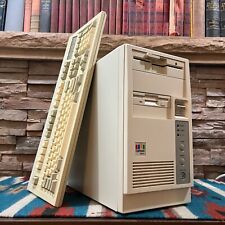
Vintage Retro AT PC Tower - Intel 486 4MB 3.5" 5.25" OPL Sound Keyboard POSTS
$199.00
$150.00
Vintage Comfort Keyboard Systems Ergomagic Mechanical AT/PS2 Keyboard
$149.99
|
||
|
No Discussions have been posted on this vulnerability. |