|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Ubuntu Local Security Checks >> USN65-1 : apache vulnerabilities Vulnerability Assessment Details
|
USN65-1 : apache vulnerabilities |
||
|
apache vulnerabilities Detailed Explanation for this Vulnerability Assessment Summary : These remote packages are missing security patches : - apache - apache-common - apache-dbg - apache-dev - apache-doc - apache-perl - apache-ssl - apache-utils - libapache-mod-perl Description : Javier Fernández-Sanguino Peña noticed that the "check_forensic" script created temporary files in an insecure manner. This could permit a symbolic link attack to create or overwrite arbitrary files with the rights of the user invoking the program. Solution : Upgrade to : - apache-1.3.31-6ubuntu0.4 (Ubuntu 4.10) - apache-common-1.3.31-6ubuntu0.4 (Ubuntu 4.10) - apache-dbg-1.3.31-6ubuntu0.4 (Ubuntu 4.10) - apache-dev-1.3.31-6ubuntu0.4 (Ubuntu 4.10) - apache-doc-1.3.31-6ubuntu0.4 (Ubuntu 4.10) - apache-perl-1.3.31-6ubuntu0.4 (Ubuntu 4.10) - apache-ssl-1.3.31-6ubuntu0.4 (Ubuntu 4.10) - apache-utils-1.3.31-6ubuntu0.4 (Ubuntu 4.10) - libapache-mod-perl-1.29.0.2-14ubuntu0.1 (Ubuntu 4.10) Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: Ubuntu Security Notice (C) 2005 Canonical, Inc. / NASL script (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Lenovo IdeaPad 5i Slim 5 16IRL8 16" (512GB SSD, Intel Core i5-1335U, 1.30GHz,...
$422.10
For Lenovo ideapad 5 15IIL05 15ARE05 15ITL05 15ALC05 Lcd Back Cover Rear Lid NEW
$49.98
Lenovo T490 14" FHD Laptop - Intel i7-8665U (1.9GHz) 16GB Ram, 512GB SSD W10Pro
$293.49
Lenovo 500w Gen 3 Laptop, 11.6" IPS Glass, N6000, 8GB, 128GB SSD, Win 11 Home
$186.99
Lenovo IP 5 16IAU7 16" 2.5K Chromebook i3-1215U 8GB Ram 128GB eMMC Chrome OS
$219.99
Lenovo Ideapad 1i 15.6" FHD Notebook Intel Core i5-1235U 8GB RAM 256GB SSD
$339.99
Lenovo Notebook IdeaPad 1 Laptop, N6000, 4GB, 128GB eMMC, Win 11 Home-Certified
$229.49
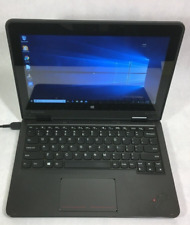
Lenovo ThinkPad Yoga 11e 11.6" 2in1 Touch Intel Core i3 4GB RAM 128GB SSD Win10
$59.00
Lenovo K14 AMD Laptop, 14" FHD IPS LED , Ryzen 5 5600U, GB, 256GB SSD
$569.00
Lenovo Thinkpad T450 14 Intel Core i5-5300U 2.30GHz 8GB RAM 256GB SSD W10 Pro
$89.94
|
||
|
No Discussions have been posted on this vulnerability. |