|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Ubuntu Local Security Checks >> USN57-1 : linux-source-2.6.8.1 vulnerabilities Vulnerability Assessment Details
|
USN57-1 : linux-source-2.6.8.1 vulnerabilities |
||
|
linux-source-2.6.8.1 vulnerabilities Detailed Explanation for this Vulnerability Assessment Summary : These remote packages are missing security patches : - linux-doc-2.6.8.1 - linux-headers-2.6.8.1-4 - linux-headers-2.6.8.1-4-386 - linux-headers-2.6.8.1-4-686 - linux-headers-2.6.8.1-4-686-smp - linux-headers-2.6.8.1-4-amd64-generic - linux-headers-2.6.8.1-4-amd64-k8 - linux-headers-2.6.8.1-4-amd64-k8-smp - linux-headers-2.6.8.1-4-amd64-xeon - linux-headers-2.6.8.1-4-k7 - linux-headers-2.6.8.1-4-k7-smp - linux-headers-2.6.8.1-4-power3 - linux-headers-2.6.8.1-4-power3-smp - linux-headers-2.6.8. [...] Description : Paul Starzetz discovered a race condition in the ELF library and a.out binary format loaders, which can be locally exploited in several different ways to gain root rights. (CVE-2004-1235) Liang Bin found a design flaw in the capability module. After this module was loaded on demand in a running system, all unprivileged user space processes got all kernel capabilities (thus essentially root rights). This is mitigated by the fact that the capability module is loaded very early in the boot process of a standard Ubuntu system, when no unprivileged user processes are yet running. (CVE-2004-1337) Finally, this update fixes a memory leak in the ip_conntrack_ftp iptables module. However, it is believed that this is not exploitable. Solution : Upgrade to : - linux-doc-2.6.8.1-2.6.8.1-16.8 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-2.6.8.1-16.8 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-386-2.6.8.1-16.8 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-686-2.6.8.1-16.8 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-686-smp-2.6.8.1-16.8 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-amd64-generic-2.6.8.1-16.8 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-amd64-k8-2.6.8.1-16.8 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-amd64-k8-smp-2.6.8.1-16.8 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-a [...] Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: Ubuntu Security Notice (C) 2005 Canonical, Inc. / NASL script (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Vintage RCA Cosmac VIP With User Manuals & TV Interface - 1802 Microprocessor
$1199.99
Vintage AST Ascentia 900N 4/50 CS10 Notebook UNTESTED no cables
$29.99
Intel Celeron 300 333 MHz SL2YP SL2X8 SL2WN SL2WN SL2Y2 vintage CPU GOLD
$10.95
AT Tower Computer Case, MEV 120 HX, CLEANED Vintage For 386/486/Pentium, READ
$99.99
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Vintage Gateway 2000 4DX-33V Desktop Computer BAD PSU READ BELOW
$200.00
Vintage Macintosh Classic Case Apple asset tag
$50.00
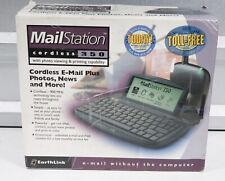
Vintage Earthlink CEDCO MailStation 350 Cordless email
$15.00
Vintage Comfort Keyboard Systems Ergomagic Mechanical AT/PS2 Keyboard
$149.99
Vintage scorpius 980n plus Mechanical USB keyboard
$39.00
|
||
|
No Discussions have been posted on this vulnerability. |