|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Ubuntu Local Security Checks >> USN39-1 : linux-source-2.6.8.1 vulnerability Vulnerability Assessment Details
|
USN39-1 : linux-source-2.6.8.1 vulnerability |
||
|
linux-source-2.6.8.1 vulnerability Detailed Explanation for this Vulnerability Assessment Summary : These remote packages are missing security patches : - linux-doc-2.6.8.1 - linux-headers-2.6.8.1-4 - linux-headers-2.6.8.1-4-386 - linux-headers-2.6.8.1-4-686 - linux-headers-2.6.8.1-4-686-smp - linux-headers-2.6.8.1-4-amd64-generic - linux-headers-2.6.8.1-4-amd64-k8 - linux-headers-2.6.8.1-4-amd64-k8-smp - linux-headers-2.6.8.1-4-amd64-xeon - linux-headers-2.6.8.1-4-k7 - linux-headers-2.6.8.1-4-k7-smp - linux-headers-2.6.8.1-4-power3 - linux-headers-2.6.8.1-4-power3-smp - linux-headers-2.6.8. [...] Description : USN-30-1 fixed several flaws in the Linux ELF binary loader's handling of setuid binaries. Unfortunately it was found that these patches were not sufficient to prevent all possible attacks on 64-bit platforms, so previous amd64 kernel images were still vulnerable to root privilege escalation if setuid binaries were run under certain conditions. This issue does not affect the i386 and powerpc platforms. Solution : Upgrade to : - linux-doc-2.6.8.1-2.6.8.1-16.4 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-2.6.8.1-16.4 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-386-2.6.8.1-16.4 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-686-2.6.8.1-16.4 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-686-smp-2.6.8.1-16.4 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-amd64-generic-2.6.8.1-16.4 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-amd64-k8-2.6.8.1-16.4 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-amd64-k8-smp-2.6.8.1-16.4 (Ubuntu 4.10) - linux-headers-2.6.8.1-4-a [...] Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: Ubuntu Security Notice (C) 2005 Canonical, Inc. / NASL script (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung 860 Evo 250GB MZ7LH250HAHQ SSD
$11.95
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Samsung - S Pen Creator Edition - White
$40.00
Samsung Galaxy Tab S7 SM-T878U 128GB, Wi-Fi + 5G (T-Mobile), 11" (Parts Only)
$129.13
Samsung PM883 960GB 2.5" MZ7LH960HAJR-00005 MZ-7LH9600 SSD SOLID STATE DRIVE
$62.99
Samsung Galaxy Chromebook Go, 14-inch, 32GB, Unlocked All Carriers - Silver
$99.95
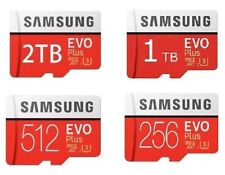
512GB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$21.99
Samsung 16GB 2Rx4 PC3-12800R M393B2G70BH0-CK0 DDR3 RDIMM - SERVER RAM
$8.90
|
||
|
No Discussions have been posted on this vulnerability. |