|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Ubuntu Local Security Checks >> USN252-1 : gnupg vulnerability Vulnerability Assessment Details
|
USN252-1 : gnupg vulnerability |
||
|
gnupg vulnerability Detailed Explanation for this Vulnerability Assessment Summary : The remote package "gnupg" is missing a security patch. Description : Tavis Ormandy discovered a potential weakness in the signature verification of gnupg. gpgv and gpg --verify returned a successful exit code even if the checked file did not have any signature at all. The recommended way of checking the result is to evaluate the status messages, but some third party applications might just check the exit code for determining whether or not a signature is valid. These applications could be tricked into erroneously reporting a valid signature. Please note that this does not affect the Ubuntu package signature checks. Solution : Upgrade to : - gnupg-1.4.1-1ubuntu1.1 (Ubuntu 5.10) Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: Ubuntu Security Notice (C) 2005 Canonical, Inc. / NASL script (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
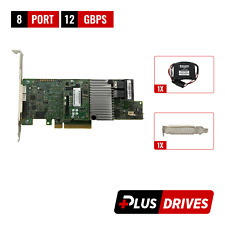
Cisco UCS LSI MegaRAID 9271CV-8I SAS2308 PCIe SAS Internal RAID Controller
$28.00
Intel PCIe SSD AIC RAID Controller Card G97168-252
$44.55
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
Oracle Sun 8-Port 6 Gbps SAS/SATA Raid Controller PCIe w/Cables 7055240 7047503
$13.49
LSI 9271-8i MegaRAID 8-Port 6Gbps PCIe RAID Controller w/ 1Gb CacheVault & BBU
$30.99
4 Bay RAID External Hard Drive Enclosure for 2.5/3.5" SATA HDD/SSD
$79.99
G TECHNOLOGY G RAID 0G04228 2-Bay Thunderbolt 2 RAID Array W/Power Supply
$99.99
|
||
|
No Discussions have been posted on this vulnerability. |