|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Ubuntu Local Security Checks >> USN133-1 : apache vulnerability Vulnerability Assessment Details
|
USN133-1 : apache vulnerability |
||
|
apache vulnerability Detailed Explanation for this Vulnerability Assessment Summary : These remote packages are missing security patches : - apache - apache-common - apache-dbg - apache-dev - apache-doc - apache-perl - apache-ssl - apache-utils - libapache-mod-perl Description : A buffer overflow was discovered in the "htpasswd" utility. This could be exploited to execute arbitrary code with the rights of the user invoking htpasswd. This is only a security vulnerability if you have a website that offers a public interface to htpasswd without checking the input beforehand however, this is very unusual. Solution : Upgrade to : - apache-1.3.31-6ubuntu0.7 (Ubuntu 4.10) - apache-common-1.3.31-6ubuntu0.7 (Ubuntu 4.10) - apache-dbg-1.3.31-6ubuntu0.7 (Ubuntu 4.10) - apache-dev-1.3.31-6ubuntu0.7 (Ubuntu 4.10) - apache-doc-1.3.31-6ubuntu0.7 (Ubuntu 4.10) - apache-perl-1.3.31-6ubuntu0.7 (Ubuntu 4.10) - apache-ssl-1.3.31-6ubuntu0.7 (Ubuntu 4.10) - apache-utils-1.3.31-6ubuntu0.7 (Ubuntu 4.10) - libapache-mod-perl-1.29.0.2.0-6ubuntu0.7 (Ubuntu 4.10) Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: Ubuntu Security Notice (C) 2005 Canonical, Inc. / NASL script (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Vintage DEC/CLEARPOINT INC. -QRAM-2 SAB-1 1MB Q-BUS MEMORY MSV11-QA (B2)
$129.99
VINTAGE DEC Digital RK11-D DISK CONTROL M7255 PDP 11 (B1)
$129.99
Vintage DEC/The Redac mini cabinet front panel Digital Equipment Corp. 19"
$269.99
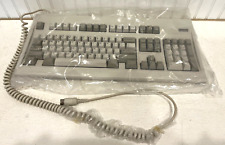
Digital Equipment Corporation DEC-2000 Vintage Keyboard - NOS NEW in Plastic
$129.95
DEC PDP 8/M PDP 8M / 4 avail / Vintage Digital Equipment Corp /Also DEC PDP 12
$5775.00
Rare Vintage DEC DIGITAL DFO3 modem with manual Powers up but UNTESTED
$69.95
Vintage Digital DEC dfo1 Acoustic Coupler modem Anderson Jacobsen Mod# A242 RARE
$195.95
Vintage DEC Digital RX 180 AB Dual 5.25" Disk Drive
$149.00
Vintage DEC Digital M8048 5013995C PDP-11 LSI 11 ROM (B3)
$79.99
DEC Digital DECMATION D100Q Z80 processor card CP/M PDP-11 (1982) B1
$119.99
|
||
|
No Discussions have been posted on this vulnerability. |