|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows : Microsoft Bulletins >> Trusting domains bad verification Vulnerability Assessment Details
|
Trusting domains bad verification |
||
|
Acertains the presence of the relevant security fixes Detailed Explanation for this Vulnerability Assessment Trust relationships are created between Windows NT or Windows 2000 domains to permit users in one domain to access resources in other domains without requiring them to authenticate separately to each domain. When a user in a trusted domain requests access to a resource in a trusting domain, the trusted domain supplies authorization data in the form of a list of Security Identifiers (SIDs) that indicate the user's identity and group memberships. The trusting domain uses this data to acertain whether to grant the user's request. A vulnerability exists because the trusting domain does not verify that the trusted domain is actually authoritative for all the SIDs in the authorization data. If one of the SIDs in the list identified a user or security group that is not in the trusted domain, the trusting domain would accept the information and use it for subsequent access control decisions. If a possible hacker inserted SIDs of his choice into the authorization data at the trusted domain, he could elevate his rights to those associated with any desired user or group, including the Domain Administrators group for the trusting domain. This would enable the attacker to gain full Domain Administrator access on computers in the trusting domain. Solution : see http://www.microsoft.com/technet/security/bulletin/ms02-001.mspx Network Security Threat Level: Medium Networks Security ID: 3997 Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Renaud Deraison |
||
|
Cables, Connectors |

Atari 600 XL Vintage Home Computer - New in Box, Unused
$200.00
Vintage Atari 800XL Computer With Original Box
$140.00
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Vintage Family owned Atari 1200xl computer sold as is tested turns on with cable
$299.99
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Vintage Atari 800XL ~ Home Computer in Original Box ~ Tested and Working
$149.90
RARE San Jose Computer Special Edition 810 5 1/4" Floppy Disc Drive Atari 8-bit
$195.00
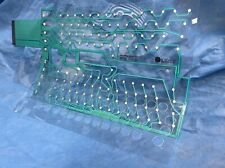
ATARI 600XL / 800XL Keyboard Membrane Replacement - NEW
$37.99
Ms. Pac-Man Game Cartridge Atari TI99/4A TI-99/4A 1983 MS PACMAN UNTESTED/AS IS
$21.24
$225.00
|
||
|
No Discussions have been posted on this vulnerability. |