|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SuSE-SA:2004:005: Linux Kernel Vulnerability Assessment Details
|
SuSE-SA:2004:005: Linux Kernel |
||
|
Check for the version of the Linux Kernel package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SuSE-SA:2004:005 (Linux Kernel). Another bug in the Kernel's do_mremap() function, which is unrelated to the bug fixed in SuSE-SA:2004:001, was found by Paul Starzetz. The do_mremap() function of the Linux Kernel is used to manage Virtual Memory Areas (VMAs) which includes moving, removing and resizing of memory areas. To remove old memory areas do_mremap() uses the function du_munmap() without checking the return value. By forcing do_munmap() to return an error the memory management of a process can be tricked into moving page table entries from one VMA to another. The destination VMA may be protected by a different ACL which enables a local attacker to gain write access to previous read-only pages. The result will be local root access to the system. Additionally to the bug mentioned above some other bugs were fixed (depending on architecture) that can cause local denial-of-service conditions: - Vicam USB driver: CVE-2004-0075 + denial-of-service due to problem while copying data from user to kernel space - Direct Render Infrastructure: CVE-2004-0003 + denial-of-service due to integer overflow + needs r128 card and console to be exploited - ncpfs/ncp_lookup: CVE-2004-0010 + buffer overflow with the probability to gain root - execve(): + malformed elf binaries can lead to a local denial-of-service attack Solution : http://www.suse.de/security/2004_05_linux_kernel.html Network Security Threat Level: High Networks Security ID: 9570, 9690, 9691 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Bare S100 CPU Replacement for ALTAIR 8800 IMSAI 8080 JAIR Single Board Computer
$42.00
MITS Altair 8800 Computer Bamboo Reproduction Arduino Tested Working Assembled
$649.99
MITS ALTAIR 8800 Original Vintage Microcomputer
$6000.00
S-100 backplane motherboard bare PCB 9 slot (for Altair/IMSAI)
$30.00
MITS ALTAIR 8800 Original Vintage Microcomputer with 14 boards - Buy It Now
$9500.00
MITS ALTAIR 8800 Original Vintage Microcomputer S-100 Buy It Now $5999
$5999.00
Altair MITS 8800 CPU Parts Kit not IMSAI 8080 S100 (board NOT included)
$64.95
1974 Early Microcomputers by MITS Altair 8800's Ed Roberts HP-9810 Mark-8 Scelbi
$55.00
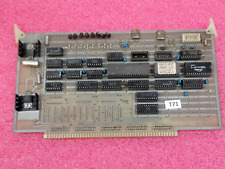
Vintage Altair 8088 CPU Wire Wrapped S100 Card w Mon EPROM circuit board #T71
$99.00
VINTAGE DEC 1975 VOL 1 ISSUE 1 SCCS INTERFACE MAGAZINE MITS ALTAIR COVER & ADS
$359.99
|
||
|
No Discussions have been posted on this vulnerability. |