|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain a shell remotely >> Shell Command Execution Vulnerability Vulnerability Assessment Details
|
Shell Command Execution Vulnerability |
||
|
Checks for the filtering of dangerous meta characters from network binded scripts Detailed Explanation for this Vulnerability Assessment The remote port seems to be running some form of shell script, with some provided user input. The input is not stripped for such meta characters as ` ' | , etc. This would permit a remote attacker to execute arbitrary code. Solution : Make sure all meta characters are filtered out, or close the port for access from untrusted networks Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2001 SecurITeam |
||
|
Cables, Connectors |

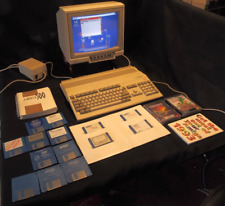
Amiga 4000/040 w/Toaster/Flyer/PAR
$2800.00
Commodore Amiga FLOPPY DRIVE EMULATOR GOTEK BLACK - WORKING
$37.95
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$37.24
Amiga 500 Gotek Custom Mount USB Floppy Emulator - Complete Kit with Gotek
$65.00
Amiga MiniMig 2.0 - FPGA Amiga 500 with real 68000CPU
$179.99
Commodore Amiga 500 with Original Box. Power Supply Games and More 1 MEG No.2
$463.19
$299.95
Commodore Amiga 1000 w/Keyboard, Mouse, RAM upgrade
$850.00
AMIGA 500 COMPUTER COMMODORE Complete in Box Powers/untested Good Condition
$370.00
Amiga 5.25 External DUAL SLIM Floppy Disk Drive VERY RARE
$199.00
|
||
|
No Discussions have been posted on this vulnerability. |