|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> SWC Overflow Vulnerability Assessment Details
|
SWC Overflow |
||
|
Searches for the existence of /cgi-bin/swc Detailed Explanation for this Vulnerability Assessment The CGI 'swc' (Simple Web Counter) is present and vulnerable to a buffer overflow when issued a too long value to the 'ctr=' argument. A possible hacker may use this flaw to gain a shell on this host Solution : Use another web counter, or patch this one by hand Reference : http://online.securityfocus.com/archive/1/76818 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2000 Renaud Deraison |
||
|
Cables, Connectors |

Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$40.44
v4.5 EPROM BOOT Chip for GVP Accelerators & SCSI Controllers for Amiga 500 2000
$9.98
Brand New Amiga 4000T Keyboard
$299.99
$49.99
Commodore Amiga 1060 Side Car Expansion "IBM PC EMULATOR" VERY RARE COLLECTIBLE
$1499.95
Apollo Vampire 600v2 / 600 V2 FPGA Accelerator Card for Commodore Amiga 600
$350.00
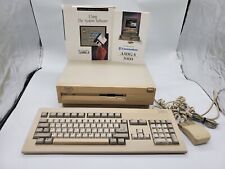
Commodore Amiga 3000 030 25Mhz + Keyboard + Mouse - Amiga OS 3.2 - WORKS 100%
$1599.99
Vintage Commodore Amiga A1000 Keyboard & Mouse - Untested - As Is - No Computers
$210.00
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
AMIGA 500 COMPUTER COMMODORE Complete in Box Powers/untested Good Condition
$370.00
|
||
|
No Discussions have been posted on this vulnerability. |