|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2007:011: acroread Vulnerability Assessment Details
|
SUSE-SA:2007:011: acroread |
||
|
Check for the version of the acroread package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2007:011 (acroread). The Adobe Acrobat Reader has been updated to version 7.0.9. This update also includes following security fixes: CVE-2006-5857: A memory corruption problem was fixed in Adobe Acrobat Reader can potentially lead to code execution. CVE-2007-0044: Universal Cross Site Request Forgery (CSRF) problems were fixed in the Acrobat Reader test which could be exploited by remote attackers to conduct CSRF attacks using any site that is providing PDFs. CVE-2007-0045: Cross site scripting problems in the Acrobat Reader test were fixed, which could be exploited by remote attackers to conduct XSS attacks against any site that is providing PDFs. CVE-2007-0046: A double free problem in the Acrobat Reader test was fixed which could be used by remote attackers to potentially execute arbitrary code. Note that all platforms using Adobe Reader currently have counter measures against such attack where it will just cause a controlled abort(). CVE-2007-0047 and CVE-2007-0048 affect only Microsoft Windows and Internet Explorer. Please note that the Acrobat Reader on SUSE Linux Enterprise Server 9 is affected too, but can not be updated currently due to GTK+ 2.4 requirements. We are trying to find a solution. Acrobat Reader on SUSE Linux Enterprise Server 8 and SUSE Linux Desktop 1 is no longer supported and should be deinstalled. Solution : http://www.suse.de/security/http://www.novell.com/linux/security/advisories/2007_11_acroread.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

NetFu Firewall 1U, Intel CPU, 8 x Gigabit, SFP, w/ pfSense, Others, NEW OPTIONS
$553.95
Fortinet FortiGate-40C Network Security Firewall
$42.50
NEW NetFu Firewall Mini, Intel CPU, 6 x Gigabit, 4gb/64gb, pfSense
$300.00
Fortinet Fortigate FG-61E | Firewall Network Security Appliance
$49.99
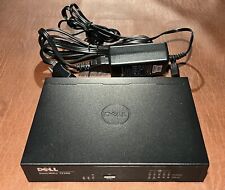
Dell SonicWall TZ300 5-Port Network Security Firewall Appliance APL28-0B4
$24.95
Fortinet FortiGate FG-40F Network Security Firewall
$100.00
Fortinet Fortigate 70D Firewall Adapter Network Security Appliance
$52.00
OPNsense six-port Gigabit router/firewall on Lanner FW-7535 hardware
$69.00
Fortinet Fortiwifi 60D FG-60D Security Appliance Firewall / VPN w/ AC Adapter
$999.97
Fortinet FortiGate 60E & FortiAP 221E+ Network Security Firewall
$260.00
|
||
|
No Discussions have been posted on this vulnerability. |