|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2006:078: clamav Vulnerability Assessment Details
|
SUSE-SA:2006:078: clamav |
||
|
Check for the version of the clamav package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2006:078 (clamav). The anti virus scan engine ClamAV has been updated to version 0.88.7 to fix various security problems: CVE-2006-5874: Clam AntiVirus (ClamAV) permits remote attackers to cause a denial of service (crash) via a malformed base64-encoded MIME attachment that triggers a null pointer dereference. CVE-2006-6481: Clam AntiVirus (ClamAV) 0.88.6 permited remote attackers to cause a denial of service (stack overflow and application crash) by wrapping many layers of multipart/mixed content around a document, a different vulnerability than CVE-2006-5874 and CVE-2006-6406. CVE-2006-6406: Clam AntiVirus (ClamAV) 0.88.6 permited remote attackers to bypass virus detection by inserting invalid characters into base64 encoded content in a multipart/mixed MIME file, as demonstrated with the EICAR test file. Solution : http://www.suse.de/security/http://www.novell.com/linux/security/advisories/2006_78_clamav.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

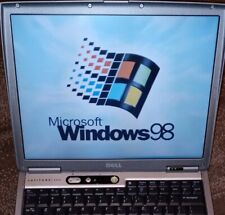
Dell Latitude D600 vintage laptop computer, 40GB HD, Windows 98 SE
$100.00
Vintage Computer Mouse - Todays Mouse - Windows 95 P S/2
$9.99
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Vintage Apple Lisa Brochure, very nice condition
$50.00
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Z80 - NABU PC & Keyboard - Vintage New Old Stock (Retro 80's)
$139.99
Vintage Black Microsoft intellimouse Optical USB Wheel Mouse 1.1/1.1a - EXC COND
$28.95
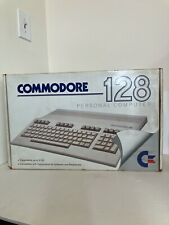
Vintage Commodore 128 Personal Computer w/Box 1987 Untested As Is Rare
$249.99
Vintage NOS Keytronic E03601Q AT/XT 5 Pin DIN Wired Computer Keyboard, SEALED
$89.99
|
||
|
No Discussions have been posted on this vulnerability. |