|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2006:039: kdebase3-kdm Vulnerability Assessment Details
|
SUSE-SA:2006:039: kdebase3-kdm |
||
|
Check for the version of the kdebase3-kdm package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2006:039 (kdebase3-kdm). The KDE Display Manager KDM stores the type of the previously used session in the user's home directory. By using a symlink a local attacker could trick kdm into also storing content of files that are normally not accessible by users, like for instance /etc/shadow. This problem is tracked by Mitre CVE ID CVE-2006-2449 and was found by Ludwig Nussel of the SUSE Security Team. Solution : http://www.suse.de/security/http://www.novell.com/linux/security/advisories/2006_39_kdm.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Samsung Galaxy Tab A 8.0" 2019 SM-T290 32GB WiFi Tablet Open Box
$94.99
SAMSUNG M393A2G40DB0-CPB 16GB PC4-17000P DDR4-2133 2RX4 ECC
$14.95
Samsung - S Pen Creator Edition - White
$40.00
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Samsung Galaxy Chromebook Go, 14-inch, 32GB, Unlocked All Carriers - Silver
$99.95
Samsung 16GB 2Rx4 PC3-12800R M393B2G70BH0-CK0 DDR3 RDIMM - SERVER RAM
$8.90
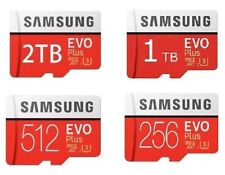
512GB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$21.99
Samsung Book Cover Keyboard Slim for Samsung Galaxy Tab S9+/S9 FE+ (5G) - Black
$65.99
|
||
|
No Discussions have been posted on this vulnerability. |