|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2006:021: MozillaFirefox,mozilla Vulnerability Assessment Details
|
SUSE-SA:2006:021: MozillaFirefox,mozilla |
||
|
Check for the version of the MozillaFirefox,mozilla package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2006:021 (MozillaFirefox,mozilla). A number of security issues have been fixed in the Mozilla browser suite and the Mozilla Firefox browser. These problems could be used by remote attackers to gain rights, gain access to confidential information or to cause denial of service attacks. The updates of the Firefox packages bring it up to Firefox 1.0.8 fix level. The updates of the Mozilla suite bring it up to Mozilla 1.7.13 fix level. Mozilla Thunderbird is also affected by some of the listed issues, but updates will be provided later due to unrelated problems. Most of them can be worked around by turning Java Script in Mails off (which is the default for Thunderbird). Full details of all issues can be found on: http://www.mozilla.org/security/announce/ List of issues that were fixed: MFSA 2006-25/CVE-2006-1727: Privilege escalation through Print Preview MFSA 2006-24/CVE-2006-1728: Privilege escalation using crypto.generateCRMFRequest MFSA 2006-23/CVE-2006-1729: File stealing by changing input type MFSA 2006-22/CVE-2006-1730: CSS Letter-Spacing Heap Overflow Vulnerability MFSA 2006-21/CVE-2006-0884: Javascript execution when forwarding or replying MFSA 2006-19/CVE-2006-1731 Cross-site scripting using .valueOf.call() MFSA 2006-18/CVE-2006-0749 Mozilla Firefox Tag Order Vulnerability MFSA 2006-17/CVE-2006-1732 Cross-site scripting through window.controllers MFSA 2006-16/CVE-2006-1733 Accessing XBL compilation scope via valueOf.call() MFSA 2006-15/CVE-2006-1734 Privilege escalation using a JavaScript functions cloned parent MFSA 2006-14/CVE-2006-1735 Privilege escalation via XBL.method.eval MFSA 2006-13/CVE-2006-1736 Downloading executables with 'Save Image As...' MFSA 2006-12/CVE-2006-1740 Secure-site spoof (requires security warning dialog) MFSA 2006-11/CVE-2006-1739,CVE-2006-1737,CVE-2006-1738,CVE-2006-1790 Crashes with evidence of memory corruption (rv:1.8) MFSA 2006-10/CVE-2006-1742 JavaScript garbage-collection hazard audit MFSA 2006-09/CVE-2006-1741 Cross-site JavaScript injection using event handlers We wish to thank the Mozilla Developers and the various bug reporters for reporting and fixing those issues. Solution : http://www.suse.de/security/advisories/2006_04_20.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
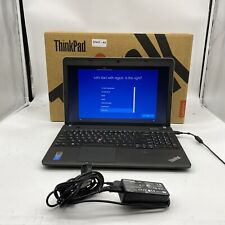
Cables, Connectors |

Lenovo IdeaPad 5i Slim 5 16IRL8 16" (512GB SSD, Intel Core i5-1335U, 1.30GHz,...
$469.00
Lenovo Ideapad Slim 1-14AST-05 | AMD A6-9220e | 4GB RAM | 64GB SSD | NO OS/CHRGR
$99.99
Lenovo Workstation Gaming NVIDIA RTX 2080 W-2135 up to 128GB RAM 4TB SSD Win11P
$739.99
Lenovo Legion 5 15.6" Gaming Laptop AMD R7 7735HS RTX 4060 16GB RAM 512GB SSD
$999.99
Lenovo ThinkPad E560 Intel Core i5-6200U 2.3GHz 8GB RAM 500GB SSD W10P w/Charger
$74.00
Lenovo ThinkPad E540 Intel i7-4702MQ 2.2GHz 16GB RAM 500GB SSD W10P w/Charger
$82.00
Lenovo ThinkPad X1 Nano 13" Touchscreen 2K i7-1180G7 16GB/256GB Win 10 Pro
$599.69
Lenovo 500w Gen 3 Laptop, 11.6" IPS Glass, N6000, 8GB, 128GB SSD, Win 11 Home
$209.99
Lenovo 2-in-1 Touchscreen Laptop/Tablet PC 11.6" Windows 10 4GB RAM 250GB SSD
$107.87
~CD/DVD DRIVE~15.6" Lenovo ThinkPad Laptop PC: Intel i5 16GB RAM 512GB SSD
$189.99
|
||
|
No Discussions have been posted on this vulnerability. |