|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2005:041: php/pear XML::RPC Vulnerability Assessment Details
|
SUSE-SA:2005:041: php/pear XML::RPC |
||
|
Check for the version of the php/pear XML::RPC package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2005:041 (php/pear XML::RPC). A bug in the PEAR::XML_RPC library permited remote attackers to pass arbitrary PHP code to the eval() function. The updated php packages fix the XML::RPC bug, however several third party PHP packages include a copy of the problematic XML::RPC code itself and might be still vulnerable after the update. Please check their respective websites whether the package is vulnerable. The following projects are known to include the XML::RPC code: - tikiwiki - postnuke - drupal - b2evolution - b2 - phpGroupWare - eGroupware - Serendipity Weblog - phpAdsNew - Max Media Manager This issue is tracked by the Mitre CVE ID CVE-2005-1921. The bug in the SUSE php packages affects SUSE Linux versions from 8.2 up to 9.3, SUSE Linux Enterprise Server 9 and Open Enterprise Server. php4 on SUSE Linux Enterprise Server 8 is not affected, since it was not shipping the XML::RPC extension. Solution : http://www.suse.de/security/advisories/2005_41_php_pear.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

MOS 6502 CPU for Commodore VIC 20 Computer & 1541 & 1571 Tested US SELLER
$12.99
$200.00
Commodore 128D Vintage Computer System Working + Manual + Keyboard [Vr RARE]
$770.64
Commodore Plus 4 Computer Complete In Box (Tested Works)
$180.00
Vintage Commodore 128 Personal Computer w/Box 1987 Untested As Is Rare
$249.99
commodore 128, 128D, 128DCR A/V Breakout
$19.99
Commodore SX-64 W/Rare 1541 Flash Installed READ DESCRIPTION SX64 C-64
$459.00
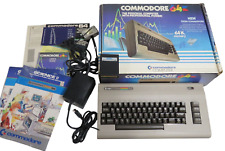
COMMODORE 64 COMPUTER (CIB) WORKING W/ POWER SUPPLY
$199.95
1984 Commodore home Computer Video Color Monitor Model 1702
$252.00
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
|
||
|
No Discussions have been posted on this vulnerability. |


![Commodore 128D Vintage Computer System Working + Manual + Keyboard [Vr RARE] picture](/store/img/g/NOYAAOSwYFFmI3Ly/s-l225/Commodore-128D-Vintage-Computer-System-Working-Man.jpg)