|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2004:045: samba Vulnerability Assessment Details
|
SUSE-SA:2004:045: samba |
||
|
Check for the version of the samba package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2004:045 (samba). The Samba developers informed us about several potential integer overflow issues in the Samba 2 and Samba 3 code. This update adds constraints to the Samba server code which protects it from using values from untrusted sources as operands in arithmetic operations to acertain heap memory space needed to copy data. Without these limitations a remote attacker may be able to overflow the heap memory of the process and to overwrite vital information structures which can be abused to execute arbitrary code. Solution : http://www.suse.de/security/advisories/2004_45_samba.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

Macintosh Platinum Mouse - Apple 128K 512K 512Ke Mac Plus Lisa IIe M0100 - NEW
$44.99
Lot Of Two Vintage Apple Macintosh Computers Models 128k M0001 For Parts
$250.00
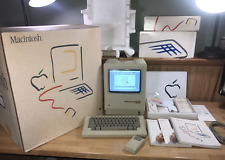
1984 APPLE MACINTOSH 128K 40th Anniversary MATCHING # BOX Set 1st Mac M0001 NICE
$7999.99
Apple Macintosh 128k 512k Plus Analog Board Capacitor Re-Cap Kit - US Shipping
$23.95
1984 Apple Macintosh 128K Mac EARLY FIRST Version RFI Foil Motherboard Shield
$29.99
Vintage Apple Macintosh Classic 128K Game Pack 3 On New 400K Double Density Disk
$39.99
1984 Apple Macintosh 128K Mac 512K RFI Foil Motherboard Shield 805-0577 REV. D
$24.99
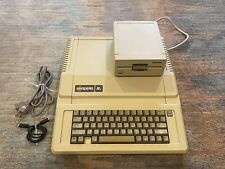
Vintage Apple lle 128k Enhanced Computer A2S2064 Rebuilt W/ Disk Drive & more
$359.99
Apple M0120 Keypad Keyboard for Macintosh 128k 512k Plus - FULLY TESTED
$99.99
Apple Macintosh 128K M0001 Computer with Mouse, no keyboard. Case included. 1984
$510.41
|
||
|
No Discussions have been posted on this vulnerability. |