|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2004:022: samba Vulnerability Assessment Details
|
SUSE-SA:2004:022: samba |
||
|
Check for the version of the samba package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2004:022 (samba). The Samba Web Administration Tool (SWAT) was found vulnerable to a buffer overflow in its base64 code. This buffer overflow can possibly be exploited remotely before any authentication took place to execute arbitrary code. The same piece of vulnerable code was also used in ldapsam passdb and in the ntlm_auth tool. This vulnerability only exists on Samba 3.0.2 to 3.0.4. Another buffer overflow was found in Samba 3.0.0 and later, as well as in Samba 2.2.x. This overflow exists in the hash code of the mangling method (smb.conf: mangling method = hash), the default uses hash2 which is not vulnerable. There is no temporary workaround known. The first proof-of-concept exploits were seen on public mailing lists. After the installation was successfully completed please restart the samba daemon. /usr/sbin/rcsmb restart SWAT is called by inetd/xinetd. Therefore it is sufficient to kill all running instances of SWAT only. Please download the update package for your distribution and verify its integrity by the methods listed in section 3) of this announcement. Then, install the package using the command 'rpm -Fhv file.rpm' to apply the update. Solution : http://www.suse.de/security/2004_22_samba.html Network Security Threat Level: High Networks Security ID: 10780 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

AUDIO CODES MP-114 VOIP Gateway Open Box
$37.49
Cisco CP-8832-K9 Unified 8800 Series Conference VOIP IP Phone 1 Year Warranty
$139.00
$199.99
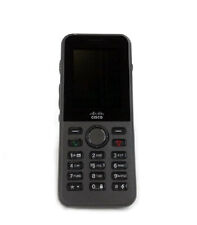
Cisco CP-8821-K9 8821 Wireless VOIP IP Phone 1 Year Waranty
$330.00
Yealink W73H IP DECT VOIP Phone
$10.00
Cisco CP-7945G VOIP Phone With Stand & Handset Business IP Phone 7945
$3.00
New Cisco 7945G IP VoIP Gigabit GIGE Telephone Phone CP-7945G -
$24.95
Grandstream GS-HT802 2 Port Analog Telephone Adapter VoIP Phone & Device, Black
$32.00
Cisco VG202XM Analog Voice Gateway VoIP -- [NEW/FULL KIT]
$76.00
LOT OF 10 Cisco CP-7841-K9 VoIP 4-Line Business Phone w/ Stand Handset Cord
$69.99
|
||
|
No Discussions have been posted on this vulnerability. |







![Cisco VG202XM Analog Voice Gateway VoIP -- [NEW/FULL KIT] picture](/store/img/g/I0YAAOSwn0lle2WJ/s-l225/Cisco-VG202XM-Analog-Voice-Gateway-VoIP-NEW-FULL-K.jpg)
