|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2002:040: lprng, html2ps Vulnerability Assessment Details
|
SUSE-SA:2002:040: lprng, html2ps |
||
|
Check for the version of the lprng, html2ps package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2002:040 (lprng, html2ps). The lprng package contains the 'runlpr' program which permits the lp user to execute the lpr program as root. Local attackers can pass certain commandline arguments to lpr running as root, fooling it to execute arbitrary commands as root. This has been fixed. Note that this vulnerability can only be exploited if the attacker has previously gained access to the lp account. Additionally, the html2ps printfilter, which is installed as part of the LPRng print system, permited remote attackers to execute arbitrary commands in the context of the lp user. These two issues combined permit attackers to mount a remote root attack. As a workaround, we recommend to uninstall the html2ps package, and restrict access to your print services to authorized hosts only. Access control to lpd is implemented by adding appropriate entries to the /etc/lpd.perms file. Please consult the lpd.perms(5) manpage, or add the single line DEFAULT REJECT to your /etc/lpd.perms file to deny access to everyone from the outside. Please download the update package for your distribution and verify its integrity by the methods listed in section 3) of this announcement. Then, install the package using the command 'rpm -Fhv file.rpm' to apply the update. Solution : http://www.suse.de/security/2002_040_lprng_html2ps.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.39
ASUS Prime Z390-A LGA 1151 Intel Z390 SATA USB 3.1 ATX Motherboard NO I/O
$99.00
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
MSI Gaming B150M BAZOOKA HDMI USB 3.1 DDR4 Socket LGA1151 Micro ATX Motherboard
$69.99
X99 LGA 2011-v3 MR9D Motherboard 8*DDR4 RAM USB 3.0 SATA3.0 M.2 for E5 V3 V4 CPU
$79.99
GIGABYTE Z790 AORUS Elite AX Gaming Motherboard | ATX LGA 1700, DDR5, WiFi 6E
$149.99
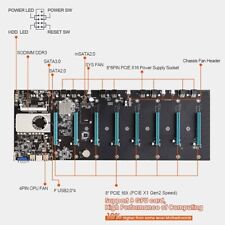
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |