|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2007-0010: koffice Vulnerability Assessment Details
|
RHSA-2007-0010: koffice |
||
|
Check for the version of the koffice packages Detailed Explanation for this Vulnerability Assessment Updated KOffice packages that fix a security issue are now available for Red Hat Enterprise Linux 2.1. This update has been rated as having moderate security impact by the Red Hat Security Response Team. KOffice is a collection of productivity applications for the K Desktop Environment (KDE) GUI desktop. An integer overflow bug was found in KOffice's PPT file processor. An attacker could create a malicious PPT file that could cause KOffice to execute arbitrary code if the file was opened by a victim. (CVE-2006-6120) All users of KOffice are advised to upgrade to these updated packages, which contains a backported patch to correct this issues. Solution : http://rhn.redhat.com/errata/RHSA-2007-0010.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

VTG Apple Macintosh Plus 1Mb Monitor Model M0001A - PARTS OR REPAIR ONLY READ
$95.00
Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
Apple Macintosh SE/30 M5119 Vintage Mac Computer BAD FLOPPY DRIVE FOR PARTS
$350.00
VINTAGE APPLE MACINTOSH POWERBOOK 180 ( M4440) Powers On
$100.00
Apple Macintosh Startup Disk for Vintage Mac - System 1.1 w/ MacWrite & MacPaint
$9.99
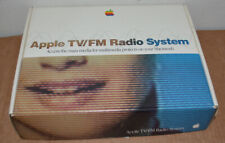
Apple MacIntosh TV FM Tuner Card In Box Complete Power PC Vintage M4586ll/a
$200.00
VINTAGE Ehman EXTERNAL SCSI MACINTOSH HARD DISK DRIVE w/HDD
$49.95
Vintage Power Computing ADB Macintosh Compatible Keyboard Membrane Untested
$29.90
VINTAGE Apple Macintosh LC (FOR PARTS - DOES NOT BOOT) NO HDD #27
$49.99
Vintage Apple Macintosh Powerbook Desktop Laptop Computer Duo Dock Model M7779
$299.99
|
||
|
No Discussions have been posted on this vulnerability. |