|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2006-0677: thunderbird Vulnerability Assessment Details
|
RHSA-2006-0677: thunderbird |
||
|
Check for the version of the thunderbird packages Detailed Explanation for this Vulnerability Assessment Updated thunderbird packages that fix several security bugs are now available for Red Hat Enterprise Linux 4. This update has been rated as having critical security impact by the Red Hat Security Response Team. Mozilla Thunderbird is a standalone mail and newsgroup client. Two flaws were found in the way Thunderbird processed certain regular expressions. A malicious HTML email could cause a crash or possibly execute arbitrary code as the user running Thunderbird. (CVE-2006-4565, CVE-2006-4566) A flaw was found in the Thunderbird auto-update verification system. An attacker who has the ability to spoof a victim's DNS could get Firefox to download and install malicious code. In order to exploit this issue an attacker would also need to get a victim to previously accept an unverifiable certificate. (CVE-2006-4567) A flaw was found in the handling of Javascript timed events. A malicious HTML email could crash the browser or possibly execute arbitrary code as the user running Thunderbird. (CVE-2006-4253) Daniel Bleichenbacher recently described an implementation error in RSA signature verification. For RSA keys with exponent 3 it is possible for an attacker to forge a signature that which would be incorrectly verified by the NSS library. (CVE-2006-4340) A flaw was found in Thunderbird that triggered when a HTML message contained a remote image pointing to a XBL script. A possible hacker could have created a carefully crafted message which would execute Javascript if certain actions were performed on the email by the recipient, even if Javascript was disabled. (CVE-2006-4570) A number of flaws were found in Thunderbird. A malicious HTML email could cause a crash or possibly execute arbitrary code as the user running Thunderbird. (CVE-2006-4571) Users of Thunderbird are advised to upgrade to this update, which contains Thunderbird version 1.5.0.7 that corrects these issues. Solution : http://rhn.redhat.com/errata/RHSA-2006-0677.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

VTG 1990s Microsoft Windows Operating System 3.1 User Guide Manual Booklet EUC
$8.00
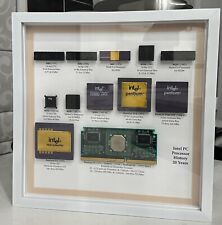
Vintage Intel Personal PC CPU Collection in White Shadowbox Display
$200.00
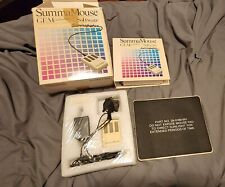
VINTAGE SummaGraphics SummaMouse
$240.00
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Z80 - NABU PC & Keyboard - Vintage New Old Stock (Retro 80's)
$139.99
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Vintage Black Microsoft intellimouse Optical USB Wheel Mouse 1.1/1.1a - EXC COND
$28.95
SEALED Vintage Western Digital Value Line Hard Drive 3.5-Inch Enhanced IDE 25 GB
$100.00
Vintage Compaq Presario Mouse, Model MUS9J, PS/2 - Tested & Working, Very Good
$12.99
|
||
|
No Discussions have been posted on this vulnerability. |