|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2006-0052: squid Vulnerability Assessment Details
|
RHSA-2006-0052: squid |
||
|
Check for the version of the squid packages Detailed Explanation for this Vulnerability Assessment An updated squid package that fixes a security vulnerability as well as several issues is now available. This update has been rated as having moderate security impact by the Red Hat Security Response Team. Squid is a high-performance proxy caching server for Web clients, supporting FTP, gopher, and HTTP data objects. A denial of service flaw was found in the way squid processes certain NTLM authentication requests. It is possible for a remote attacker to crash the Squid server by sending a specially crafted NTLM authentication request. The Common Vulnerabilities and Exposures project (cve.mitre.org) assigned the name CVE-2005-2917 to this issue. The following issues have also been fixed in this update: * An error introduced in squid-2.5.STABLE6-3.4E.12 can crash Squid when a user visits a site that has a bit longer DNS record. * An error introduced in the old package prevented Squid from returning correct information about large file systems. The new package is compiled with the IDENT lookup support so that users who want to use it do not have to recompile it. * Some authentication helpers needed SETUID rights but did not have them. If administrators wanted to use cache administrator, they had to change the SETUID bit manually. The updated package sets this bit so the new package can be updated without manual intervention from administrators. * Squid could not handle a reply from an HTTP server when the reply began with the new-line character. * An issue was discovered when a reply from an HTTP server was not HTTP 1.0 or 1.1 compliant. * The updated package keeps user-defined error pages when the package is updated and it adds new ones. All users of squid should upgrade to this updated package, which resolves these issues. Solution : http://rhn.redhat.com/errata/RHSA-2006-0052.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Dream Writer NTS 325 Computer Basic Language Notebook “Untested “
$30.00
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Datacomp DCK 84 BRAND NEW Vintage Keyboard
$39.00
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
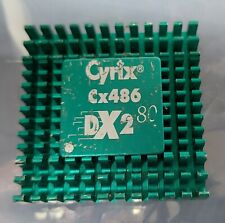
1993 Cyrix CX486 DX2-80 Processor Untested Gold Ceramic Vintage CPU
$34.99
Voltage Blaster (Enhanced) -5V ISA AT ATX Power for Vintage Retro PCs US Seller
$12.95
Vintage Black Microsoft intellimouse Optical USB Wheel Mouse 1.1/1.1a - EXC COND
$28.95
$150.00
Vintage Comfort Keyboard Systems Ergomagic Mechanical AT/PS2 Keyboard
$149.99
|
||
|
No Discussions have been posted on this vulnerability. |