|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2006-0016: initscripts Vulnerability Assessment Details
|
RHSA-2006-0016: initscripts |
||
|
Check for the version of the initscripts packages Detailed Explanation for this Vulnerability Assessment An updated initscripts package that fixes a privilege escalation issue and several bugs is now available. This update has been rated as having moderate security impact by the Red Hat Security Response Team. The initscripts package contains the basic system scripts used to boot your Red Hat system, change runlevels, and shut the system down cleanly. Initscripts also contains the scripts that activate and deactivate most network interfaces. A bug was found in the way initscripts handled various environment variables when the /sbin/service command is run. It is possible for a local user with permissions to execute /sbin/service via sudo to execute arbitrary commands as the 'root' user. The Common Vulnerabilities and Exposures project (cve.mitre.org) assigned the name CVE-2005-3629 to this issue. The following issues have also been fixed in this update: * extraneous characters were logged on bootup * fsck was attempted on file systems marked with _netdev in rc.sysinit before they were available * the dynamically-linked /sbin/multipath was called instead of the correct /sbin/multiplath.static Additionally, this update includes support for partitioned multipath devices and a technology preview of static IP over InifiniBand. All users of initscripts should upgrade to this updated package, which resolves these issues. Solution : http://rhn.redhat.com/errata/RHSA-2006-0016.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Cisco SG95-16 16-Port Gigabit Switch SG95-16-KR
$47.00
8 Ports Unmanaged Industrial Ethernet Switch Network Gigabit Ethernet Switch
$76.50
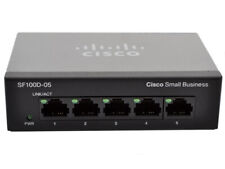
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
100Mbps Fiber Optic Media Converter 16 SC Optical Port 2 RJ45 10/100/1000Mbps
$462.99
HP 2530-48G 48 Port Gigabit Ethernet Network Switch J9775A
$30.95
New Linksys SE3005 5-port Gigabit Ethernet Switch
$18.99
Linksys SE3008 8 Ports Rack Mountable Gigabit Ethernet Switch
$21.99
HP ProCurve 2530-24G J9776A 24 Port Gigabit Ethernet Managed Network Switch
$34.99
Juniper Networks EX3300-48P 48-Port PoE+ 4x SFP+ Network Switch w/ Power Cord
$43.95
Netgear Prosafe Plus JGS524PE 24 Port Gigabit Switch 12 Port PoE JGS524PE-100NAS
$129.98
|
||
|
No Discussions have been posted on this vulnerability. |