|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2005-639: kdenetwork Vulnerability Assessment Details
|
RHSA-2005-639: kdenetwork |
||
|
Check for the version of the kdenetwork packages Detailed Explanation for this Vulnerability Assessment Updated kdenetwork packages to correct a security flaw in Kopete are now available for Red Hat Enterprise Linux 4. This update has been rated as having critical security impact by the Red Hat Security Response Team. The kdenetwork package contains networking applications for the K Desktop Environment. Kopete is a KDE instant messenger which supports a number of protocols including ICQ, MSN, Yahoo, Jabber, and Gadu-Gadu. Multiple integer overflow flaws were found in the way Kopete processes Gadu-Gadu messages. A remote attacker could send a specially crafted Gadu-Gadu message which would cause Kopete to crash or possibly execute arbitrary code. The Common Vulnerabilities and Exposures project assigned the name CVE-2005-1852 to this issue. In order to be affected by this issue, a user would need to have registered with Gadu-Gadu and be signed in to the Gadu-Gadu server in order to receive a malicious message. In addition, Red Hat believes that the Exec-shield technology (enabled by default in Red Hat Enterprise Linux 4) would block attempts to remotely exploit this vulnerability. Note that this issue does not affect Red Hat Enterprise Linux 2.1 or 3. Users of Kopete should update to these packages which contain a patch to correct this issue. Solution : http://rhn.redhat.com/errata/RHSA-2005-639.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

DEC DIGITAL Equipment Corp VT220-D2 Vintage CRT Terminal
$215.00
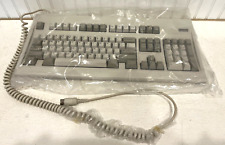
Digital Equipment Corporation DEC-2000 Vintage Keyboard - NOS NEW in Plastic
$129.95
DEC PDP 8/M PDP 8M / 4 avail / Vintage Digital Equipment Corp /Also DEC PDP 12
$5775.00
Vintage DEC Digital RX 180 AB Dual 5.25" Disk Drive
$149.00
Vintage Digital DEC dfo1 Acoustic Coupler modem Anderson Jacobsen Mod# A242 RARE
$195.95
Vintage DEC/CLEARPOINT INC. -QRAM-2 SAB-1 1MB Q-BUS MEMORY MSV11-QA (B2)
$129.99
Rare Vintage DEC DIGITAL DFO3 modem with manual Powers up but UNTESTED
$69.95
Vintage DEC Digital HiNote VP TS30G Laptop AS-IS READ Tested with external mon
$80.00
VINTAGE DEC Digital RK11-D DISK CONTROL M7255 PDP 11 (B1)
$129.99
Vintage DEC Digital M8048 5013995C PDP-11 LSI 11 ROM (B3)
$79.99
|
||
|
No Discussions have been posted on this vulnerability. |