|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2005-395: net Vulnerability Assessment Details
|
RHSA-2005-395: net |
||
|
Check for the version of the net packages Detailed Explanation for this Vulnerability Assessment Updated net-snmp packages that fix two security issues and various bugs are now available. This update has been rated as having low security impact by the Red Hat Security Response Team. SNMP (Simple Network Management Protocol) is a protocol used for network management. A denial of service bug was found in the way net-snmp uses network stream protocols. It is possible for a remote attacker to send a net-snmp agent a specially crafted packet that will crash the agent. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2005-2177 to this issue. An insecure temporary file usage bug was found in net-snmp's fixproc command. It is possible for a local user to modify the content of temporary files used by fixproc that can lead to arbitrary command execution. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2005-1740 to this issue. Additionally, the following bugs have been fixed: - The lmSensors are correctly recognized, snmp deamon no longer segfaults - The larger swap partition sizes are correctly reported - Querying hrSWInstalledLastUpdateTime no longer crashes the snmp deamon - Fixed error building ASN.1 representation - The 64-bit network counters correctly wrap - Large file systems are correctly handled - Snmptrapd initscript correctly reads options from its configuration file /etc/snmp/snmptrapd.options - Snmp deamon no longer crashes when restarted using the agentX protocol - snmp daemon now reports gigabit Ethernet speeds correctly - MAC adresses are shown when requested instead of IP adresses All users of net-snmp should upgrade to these updated packages, which resolve these issues. Solution : http://rhn.redhat.com/errata/RHSA-2005-395.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
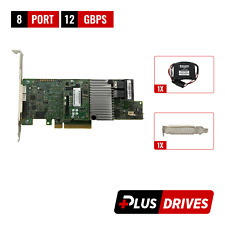
LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
HPE 727263-003 BL460c G9 Raid BBWC Smartstorage Battery
$24.99
HPE 869102-001 Smart Array E208i-a SR Gen10 Storage Controller RAID SP: 871039
$116.99
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
4 Bay RAID External Hard Drive Enclosure for 2.5/3.5" SATA HDD/SSD
$79.99
2 Bay RAID Hard Drive Enclosure USB 3.0 Type-B for 2.5" SATA SSD/HDD Enclosure
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |