|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2005-009: arts Vulnerability Assessment Details
|
RHSA-2005-009: arts |
||
|
Check for the version of the arts packages Detailed Explanation for this Vulnerability Assessment Updated kdelib and kdebase packages that resolve several security issues are now available. The kdelibs packages include libraries for the K Desktop Environment. The kdebase packages include core applications for the K Desktop Environment. Secunia Research discovered a window injection spoofing vulnerability affecting the Konqueror web browser. This issue could permit a malicious website to show arbitrary content in a different browser window. The Common Vulnerabilities and Exposures project has assigned the name CVE-2004-1158 to this issue. A bug was discovered in the way kioslave handles URL-encoded newline (%0a) characters before the FTP command. It is possible that a specially crafted URL could be used to execute any ftp command on a remote server, or potentially send unsolicited email. The Common Vulnerabilities and Exposures project has assigned the name CVE-2004-1165 to this issue. A bug was discovered that can crash KDE screensaver under certain local circumstances. This could permit a possible hacker with physical access to the workstation to take over a locked desktop session. Please note that this issue only affects Red Hat Enterprise Linux 2.1. The Common Vulnerabilities and Exposures project has assigned the name CVE-2005-0078 to this issue. All users of KDE are advised to upgrade to this updated packages, which contain backported patches to correct these issues. Solution : http://rhn.redhat.com/errata/RHSA-2005-009.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$40.46
Commodore Amiga 500C Mouse, Golden Image, PNW READ DESCRIPTION
$38.99
$4.95
$4.95
Commodore Amiga 2000 2000HD 2500 Motherboard rev4.1 ASIS for Parts or Repair
$189.98
$4.95
COMMODORE AMIGA - WORKBENCH 2.05
$4.95
Commodore C64 C128 CMD FD2000 3 1/2" Floppy Disk Drive -Complete and Functional
$700.00
AMIGA 500 COMPUTER COMMODORE Complete in Box Powers/untested Good Condition
$380.00
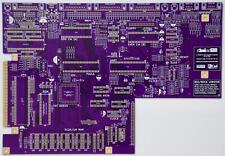
Raemixx500 Commodore Amiga500+ V2 Remake PCB Gold Plated
$35.06
|
||
|
No Discussions have been posted on this vulnerability. |