|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2004-674: acroread Vulnerability Assessment Details
|
RHSA-2004-674: acroread |
||
|
Check for the version of the acroread packages Detailed Explanation for this Vulnerability Assessment An updated Adobe Acrobat Reader package that fixes a security issue is now available. The Adobe Acrobat Reader browser permits for the viewing, distributing, and printing of documents in portable document format (PDF). iDEFENSE has reported that Adobe Acrobat Reader 5.0.9 contains a buffer overflow when decoding email messages. A possible hacker could create a malicious PDF file which could execute arbitrary code if opened by a victim. The Common Vulnerabilities and Exposures project has assigned the name CVE-2004-1152 to this issue. All users of Acrobat Reader are advised to upgrade to this updated package, which contains Acrobat Reader version 5.0.10 which is not vulnerable to this issue. Solution : http://rhn.redhat.com/errata/RHSA-2004-674.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Vintage 1991 NOS Kid Pix KidPix Studio Deluxe MS/PC-DOS 2.11 Software Broderbund
$60.00
Vintage Computer Mouse - Todays Mouse - Windows 95 P S/2
$9.99
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Z80 - NABU PC & Keyboard - Vintage New Old Stock (Retro 80's)
$139.99
Vintage Black Microsoft intellimouse Optical USB Wheel Mouse 1.1/1.1a - EXC COND
$28.95
Vintage MICROSOFT WINDOWS 2000 SP3 NO COA SEALED NEW PACKAGE with CD
$7.00
Vintage Commodore 128 Personal Computer w/Box 1987 Untested As Is Rare
$249.99
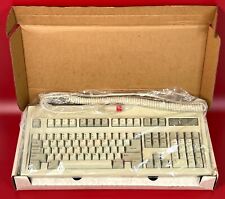
Vintage NOS Keytronic E03601Q AT/XT 5 Pin DIN Wired Computer Keyboard, SEALED
$89.99
|
||
|
No Discussions have been posted on this vulnerability. |