|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2004-654: squirrelmail Vulnerability Assessment Details
|
RHSA-2004-654: squirrelmail |
||
|
Check for the version of the squirrelmail packages Detailed Explanation for this Vulnerability Assessment An updated SquirrelMail package that fixes a cross-site scripting vulnerability is now available. SquirrelMail is a webmail package written in PHP. A cross-site scripting bug has been found in SquirrelMail. This issue could permit a possible hacker to send a mail with a carefully crafted header, which could result in causing the victim's machine to execute a malicious script. The Common Vulnerabilities and Exposures project has assigned the name CVE-2004-1036 to this issue. Additionally, the following issues have been addressed: - updated splash screens - HIGASHIYAMA Masato's patch to improve Japanese support - real 1.4.3a tarball - config_local.php and default_pref in /etc/squirrelmail/ to match upstream RPM. Please note that it is possible that upgrading to this package may remove your SquirrelMail configuration files due to a bug in the RPM package. Upgrading will prevent this from happening in the future. Users of SquirrelMail are advised to upgrade to this updated package which contains a patched version of SquirrelMail version 1.43a and is not vulnerable to these issues. Solution : http://rhn.redhat.com/errata/RHSA-2004-654.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Atari 800 Computer W/ Atari 810 Disk Drive Game Cartridge 100 Working Condition
$269.00
Atari 820 Printer for Atari Computers 400 800 600XL 800XL 1200XL 130XE
$300.00
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
RARE San Jose Computer Special Edition 810 5 1/4" Floppy Disc Drive Atari 8-bit
$200.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Atari 600XL, 800XL, 65XE, 130XE USB Power Cable - 3 ft.
$20.00
Atari 600XL, 800XL, 65XE, 130XE USB Power Cable - 3 ft.
$18.00
Atari Retro Gaming Kit for Raspberry Pi 3
$70.00
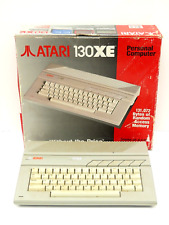
Atari 130XE Personal Retro Gaming Computer PC Complete in Original Box
$299.99
|
||
|
No Discussions have been posted on this vulnerability. |