|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2004-392: php Vulnerability Assessment Details
|
RHSA-2004-392: php |
||
|
Check for the version of the php packages Detailed Explanation for this Vulnerability Assessment Updated php packages that fix various security issues are now available. PHP is an HTML-embedded scripting language commonly used with the Apache HTTP server. Stefan Esser discovered a flaw when memory_limit is enabled in versions of PHP 4 before 4.3.8. If a remote attacker could force the PHP interpreter to allocate more memory than the memory_limit setting before script execution begins, then the attacker may be able to supply the contents of a PHP hash table remotely. This hash table could then be used to execute arbitrary code as the 'apache' user. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2004-0594 to this issue. This issue has a higher risk when PHP is running on an instance of Apache which is vulnerable to CVE-2004-0493. For Red Hat Enterprise Linux 3, this Apache memory exhaustion issue was fixed by a previous update, RHSA-2004:342. It may also be possible to exploit this issue if using a non-default PHP configuration with the "register_defaults" setting is changed to "On". Red Hat does not believe that this flaw is exploitable in the default configuration of Red Hat Enterprise Linux 3. Stefan Esser discovered a flaw in the strip_tags function in versions of PHP before 4.3.8. The strip_tags function is commonly used by PHP scripts to prevent Cross-Site-Scripting attacks by removing HTML tags from user-supplied form data. By embedding NUL bytes into form data, HTML tags can in some cases be passed intact through the strip_tags function, which may permit a Cross-Site-Scripting attack. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2004-0595 to this issue. All users of PHP are advised to upgrade to these updated packages, which contain backported patches that address these issues. Solution : http://rhn.redhat.com/errata/RHSA-2004-392.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

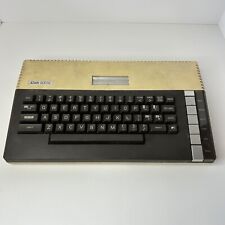
Vintage Atari 800XL Computer Powers On Untested - NO CABLES OR ACCESSORIES
$124.87
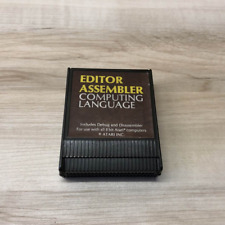
EDITOR ASSEMBLER : Computing Language Original ATARI 400/800 Computer Cartridge
$40.00
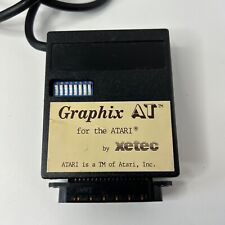
Vintage Retro Graphix AT Xetec Printer Interface Atari Computer 400 800 1200 XE
$24.72
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
A8PicoCart Kit Atari XE XL unocart clone multicart cartridge game
$18.95
Vintage Atari 800XL Computer With Original Box
$140.00
Rare Vintage Atari XF551 Floppy Disk Drive Station for 400, 800, 600, XE and XL
$300.00
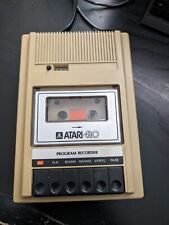
Atari 410 Program Cassette Recorder Clean Tested for power/4 cassettes/Cover
$22.99
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
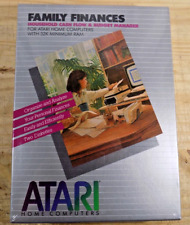
ATARI Home Computers FAMILY FINANCES Software **SEALED NEW** 1982
$25.00
|
||
|
No Discussions have been posted on this vulnerability. |