|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2004-019: mailman Vulnerability Assessment Details
|
RHSA-2004-019: mailman |
||
|
Check for the version of the mailman packages Detailed Explanation for this Vulnerability Assessment Updated mailman packages that close a DoS vulnerability present in mailman versions prior to version 2.1 are now available. Mailman is a mailing list manager. Matthew Galgoci of Red Hat discovered a Denial of Service (DoS) vulnerability in versions of Mailman prior to 2.1. A possible hacker could send a carefully-crafted message causing mailman to crash. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2003-0991 to this issue. Users of Mailman are advised to upgrade to the erratum packages, which include a backported security fix and are not vulnerable to this issue. Red Hat would like to thank Barry Warsaw for providing a patch for this issue. Solution : http://rhn.redhat.com/errata/RHSA-2004-019.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Macintosh Platinum Mouse - Apple 128K 512K 512Ke Mac Plus Lisa IIe M0100 - NEW
$44.99
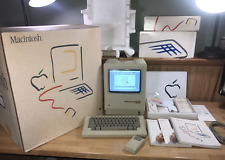
1984 APPLE MACINTOSH 128K 40th Anniversary MATCHING # BOX Set 1st Mac M0001 NICE
$7999.99
Apple Macintosh 128k 512k Plus Analog Board Capacitor Re-Cap Kit - US Shipping
$23.95
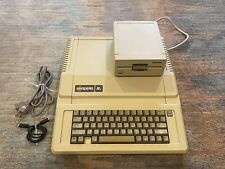
Vintage Apple lle 128k Enhanced Computer A2S2064 Rebuilt W/ Disk Drive & more
$359.99
Apple Macintosh 128K M0001 Computer 1984 W/Mouse, Keyboard, Bag & Disks AS IS
$699.00
1984 APPLE MACINTOSH Model M0001 1st MAC 128K 40th Anniversary PICASSO KIT NICE
$4999.99
Apple Macintosh M0001 128K computer & M0110 keyboard/mouse, for parts/repair
$300.00
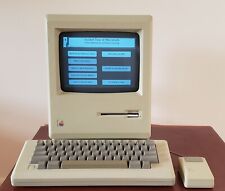
Working 1984 Apple Mac Macintosh 128K M0001 - Restored/Serviced/Tested
$1390.06
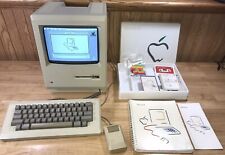
NEW 1984 Apple Macintosh 128K BOXED Model M0130 400K Mac Disk Drive UNUSED RARE
$999.95
1984 Apple Macintosh 128K Mac 512K M0110 Keyboard SPACE BAR Key and Spring ONLY
$39.95
|
||
|
No Discussions have been posted on this vulnerability. |