|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2004-004: cvs Vulnerability Assessment Details
|
RHSA-2004-004: cvs |
||
|
Check for the version of the cvs packages Detailed Explanation for this Vulnerability Assessment Updated cvs packages closing a vulnerability that could permit cvs to attempt to create files and directories in the root file system are now available. CVS is a version control system frequently used to manage source code repositories. A flaw was found in versions of CVS prior to 1.11.10 where a malformed module request could cause the CVS server to attempt to create files or directories at the root level of the file system. However, normal file system permissions would prevent the creation of these misplaced directories. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2003-0977 to this issue. Users of CVS are advised to upgrade to these erratum packages, which contain a patch correcting this issue. For Red Hat Enterprise Linux 2.1, these updates also fix an off-by-one overflow in the CVS PreservePermissions code. The PreservePermissions feature is not used by default (and can only be used for local CVS). The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2002-0844 to this issue. Solution : http://rhn.redhat.com/errata/RHSA-2004-004.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
GIGABYTE B560M DS3H AC LGA1200 Intel B560 SATA 6Gb/s Micro ATX Intel Motherboard
$64.99
Asus Prime H310M-A R2.0 Intel LGA 1151 DDR4 Desktop Motherboard
$46.99
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$48.70
GIGABYTE MB10-Datto Motherboard Xeon D-1521- SR2DF 2.40 GHz- Open Box
$112.00
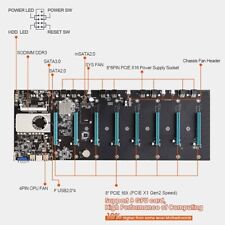
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |