|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2003-386: freeradius Vulnerability Assessment Details
|
RHSA-2003-386: freeradius |
||
|
Check for the version of the freeradius packages Detailed Explanation for this Vulnerability Assessment Updated FreeRADIUS packages are now available that fix a denial of service vulnerability. FreeRADIUS is an Internet authentication daemon, which implements the RADIUS protocol. It permits Network Access Servers (NAS boxes) to perform authentication for dial-up users. The rad_decode function in FreeRADIUS 0.9.2 and earlier permits remote attackers to cause a denial of service (crash) via a short RADIUS string attribute with a tag, which causes memcpy to be called with a -1 length argument, as demonstrated using the Tunnel-Password attribute. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2003-0967 to this issue. Users of FreeRADIUS are advised to upgrade to these erratum packages containing FreeRADIUS 0.9.3 which is not vulnerable to these issues. Solution : http://rhn.redhat.com/errata/RHSA-2003-386.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
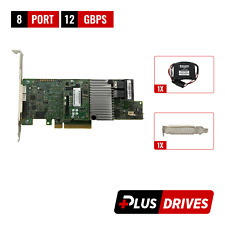
Cables, Connectors |

Intel PCIe SSD AIC RAID Controller Card G97168-252
$44.55
LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
Cisco UCS LSI MegaRAID 9271CV-8I SAS2308 PCIe SAS Internal RAID Controller
$28.00
Dell HBA330 12GBPS SAS Internal HBA Controller (NON-RAID) PCIe Card J7TNV 0J7TNV
$40.95
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$87.99
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
4 Bay RAID External Hard Drive Enclosure for 2.5/3.5" SATA HDD/SSD
$79.99
G TECHNOLOGY G RAID 0G04228 2-Bay Thunderbolt 2 RAID Array W/Power Supply
$99.99
|
||
|
No Discussions have been posted on this vulnerability. |