|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2003-244: apache Vulnerability Assessment Details
|
RHSA-2003-244: apache |
||
|
Check for the version of the apache packages Detailed Explanation for this Vulnerability Assessment Updated Apache and mod_ssl packages that fix several minor security issues are now available for Red Hat Enterprise Linux. The Apache HTTP server is a powerful, full-featured, efficient, and freely-available Web server. Ben Laurie found a bug in the optional renegotiation code in mod_ssl which can cause cipher suite restrictions to be ignored. This is triggered if optional renegotiation is used (SSLOptions +OptRenegotiate) along with verification of client certificates and a change to the cipher suite over the renegotiation. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2003-0192 to this issue. Apache does not filter terminal escape sequences from its error logs, which could make it easier for attackers to insert those sequences into terminal emulators containing vulnerabilities related to escape sequences. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2003-0020 to this issue. It is possible to get Apache 1.3 to get into an infinite loop handling internal redirects and nested subrequests. A patch for this issue adds a new LimitInternalRecursion directive. All users of the Apache HTTP Web Server are advised to upgrade to the applicable errata packages, which contain back-ported fixes correcting these issues. After the errata packages are installed, restart the Web service by running the following command: /sbin/service httpd restart Solution : http://rhn.redhat.com/errata/RHSA-2003-244.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

SD2IEC SD Card Reader for Commodore 64 ,1541 Disk Drive Emulator C64 C128 VIC
$64.95
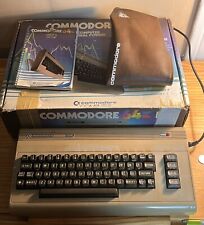
Commodore Vic 20 personal computer + box + power cords VINTAGE...FULL FUNCTION
$128.99
Apollo Vampire 600v2 / 600 V2 FPGA Accelerator Card for Commodore Amiga 600
$350.00
Vintage Commodore 64 1541 5.25" Single Floppy Disk Drive w/ Cables TESTED WORKS
$75.00
Commodore 64 C64 8 bit Home Computer Silver Label w/Power Supply KL
$224.99
Vintage Commodore MPS801 Matrix Printer W/ Manual
$51.00
Commodore 64 LOT (Computer, Box, Adaptor, Manual, Cover) FOR PARTS OR REPAIR
$200.00
Commodore CM-141 Color Monitor Tested, Works RARE
$299.99
1984 Commodore home Computer Video Color Monitor Model 1702
$275.00
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
|
||
|
No Discussions have been posted on this vulnerability. |