|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2003-231: semi Vulnerability Assessment Details
|
RHSA-2003-231: semi |
||
|
Check for the version of the semi package Detailed Explanation for this Vulnerability Assessment The remote host has an old version of the semi package installed. semi is a MIME library for GNU Emacs and XEmacs, which is used by the wl mail package. There is a vulnerability in version 1.14.3 and earlier of this software which may permit a possible hacker to overwrite arbitrary files on the remote system with the rights of the user reading his mail with wl. To exploit this flaw, a possible hacker would need to send a carefully crafted MIME encoded email to a victim on the remote host, and wait for him to open it using wl. Solution : https://rhn.redhat.com/errata/RHSA-2003-231.html Network Security Threat Level: High Networks Security ID: 8115 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
***NEW*** BCM RX67Q mATX Gaming Motherboard Combo | Intel i5-3470 | 16GB DDR3
$49.77
ASUS TUF Gaming B650-PLUS Wi-Fi Socket LGA 1700 AMD ATX Gaming Motherboard
$80.00
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
ASUS ROG Strix B650E-F Gaming WiFi AM5 ATX AMD Motherboard
$115.00
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.39
ASUS ROG STRIX B450-F GAMING AM4 AMD Motherboard
$80.00
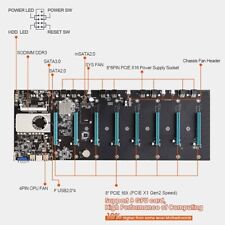
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
GIGABYTE MB10-Datto Motherboard Xeon D-1521- SR2DF 2.40 GHz- Open Box
$115.00
|
||
|
No Discussions have been posted on this vulnerability. |