|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2003-167: lv Vulnerability Assessment Details
|
RHSA-2003-167: lv |
||
|
Check for the version of the lv packages Detailed Explanation for this Vulnerability Assessment Updated lv packages that fix the possibility of local privilege escalation are now available. Lv is a powerful file viewer similar to less. It can decode and encode multilingual streams through many coding systems, such as ISO-8859, ISO-2022, EUC, SJIS Big5, HZ, and Unicode. A bug has been found in versions of lv that read a .lv file in the current working directory. Any user who subsequently runs lv in that directory and uses the v (edit) command can be forced to execute an arbitrary program. Users are advised to upgrade to these erratum packages, which contain a version of lv that is patched to read the .lv configuration file only in the user's home directory. Solution : http://rhn.redhat.com/errata/RHSA-2003-167.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Dream Writer NTS 325 Computer Basic Language Notebook “Untested “
$30.00
Apple II GS A2S6000 Vintage Computer Powers On
$125.00
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Datacomp DCK 84 BRAND NEW Vintage Keyboard
$39.00
Vintage Apple LisaDraw Brochure, very nice condition
$40.00
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
M&M's Data Pro Organizer Touch Screen With Pen Vintage RARE FIND NEW SEALED
$45.00
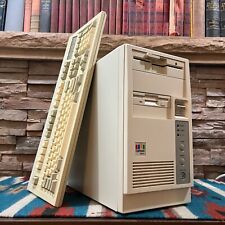
Vintage Retro AT PC Tower - Intel 486 4MB 3.5" 5.25" OPL Sound Keyboard POSTS
$199.00
Vintage PC USA & PC Globe 3.0 5.25” Floppy Disk Demos 1990 PC Globe Inc.
$15.00
Vintage Mid AT Computer Tower Case with PSU + CD Drives/Floppy
$74.99
|
||
|
No Discussions have been posted on this vulnerability. |