|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2002-157: openssl Vulnerability Assessment Details
|
RHSA-2002-157: openssl |
||
|
Check for the version of the openssl packages Detailed Explanation for this Vulnerability Assessment Updated OpenSSL packages are available which fix several serious buffer overflow vulnerabilities. OpenSSL is a commercial-grade, full-featured, and Open Source toolkit which implements the Secure Sockets Layer (SSL v2/v3) and Transport Layer Security (TLS v1) protocols as well as a full-strength general purpose cryptography library. A security audit of the OpenSSL code sponsored by DARPA found several buffer overflows in OpenSSL which affect versions 0.9.7 and 0.9.6d and earlier: 1. The master key supplied by a client to an SSL version 2 server could be oversized, causing a stack-based buffer overflow. This issue is remotely exploitable. Services that have SSLv2 disabled would not be vulnerable to this issue. (CVE-2002-0656) 2. The SSLv3 session ID supplied to a client from a malicious server could be oversized and overrun a buffer. This issue looks to be remotely exploitable. (CVE-2002-0656) 3. Various buffers used for storing ASCII representations of integers were too small on 64 bit platforms. This issue may be exploitable. (CVE-2002-0655) A further issue was found in OpenSSL 0.9.7 that does not affect versions of OpenSSL shipped with Red Hat Linux (CVE-2002-0657). A large number of applications within Red Hat Linux make use the OpenSSL library to provide SSL support. All users are therefore advised to upgrade to the errata OpenSSL packages, which contain patches to correct these vulnerabilities. NOTE: Please read the Solution section below as it contains instructions for making sure that all SSL-enabled processes are restarted after the update is applied. Thanks go to the OpenSSL team and Ben Laurie for providing patches for these issues. Solution : http://rhn.redhat.com/errata/RHSA-2002-157.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

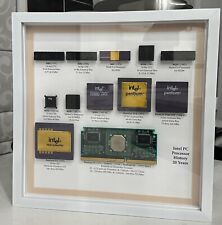
Vintage Intel Personal PC CPU Collection in White Shadowbox Display
$200.00
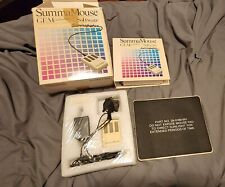
VINTAGE SummaGraphics SummaMouse
$240.00
Vintage Apple Macintosh Plus 1Mb 60W 120VAC Desktop Computer SET M0001A Tested
$499.99
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Z80 - NABU PC & Keyboard - Vintage New Old Stock (Retro 80's)
$139.99
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Vintage Black Microsoft intellimouse Optical USB Wheel Mouse 1.1/1.1a - EXC COND
$28.95
SEALED Vintage Western Digital Value Line Hard Drive 3.5-Inch Enhanced IDE 25 GB
$100.00
Vintage Compaq Presario Mouse, Model MUS9J, PS/2 - Tested & Working, Very Good
$12.99
|
||
|
No Discussions have been posted on this vulnerability. |