|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Post-Nuke information disclosure (2) Vulnerability Assessment Details
|
Post-Nuke information disclosure (2) |
||
|
Determine if a remote host is vulnerable to the opendir.php vulnerability Detailed Explanation for this Vulnerability Assessment The remote host is running post-nuke. It is possible to use it to acertain the full path to its installation on the server or the name of the database used, by doing a request like : /modules.php?op=modload&name=Sections&file=index&req=viewarticle&artid= A possible hacker may use these flaws to gain a more intimate knowledge of the remote host. Solution : Change the members list rights to admins only, or disable the members list module completely Network Security Threat Level: Low Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Tenable Network Security |
||
|
Cables, Connectors |

Vintage 5362 IBM System/36 Mini-Computer Mainframe 5291 2, CRT Terminal DM12N501
$249.99
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection - UNTESTED
$65.00
6 Vintage Computer Tape Reels mainframe 3200 5000 data ibm magnetic processor
$99.00
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection
$145.99
VINTAGE IBM Type 4869 External 5 1/4" ~ Floppy Disk Drive Mainframe ~
$159.99
Digital DEC LK201AA Terminal Keyboard RJ11 Connection Mainframe in original Box
$94.95
Cray Research Supercomputer Cray X-MP ECL Logic Board
$149.99
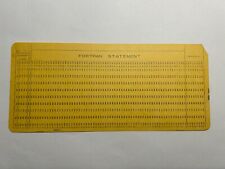
2 - VINTAGE MAINFRAME Fortran Format Punch Cards - IBM 80 columns
$3.49
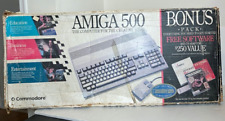
Commodore Amiga 500 Computer w/Mouse and Amiga A520 RF Modulator As Is Untested
$299.99
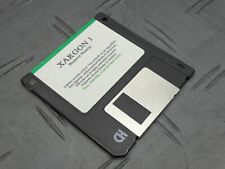
Xargon 1 Beyond Reality RARE Game Floppy 3.5” Floppy Mainframe Collection
$349.99
|
||
|
No Discussions have been posted on this vulnerability. |